Discover how a bimodal integration strategy can address the major data management challenges facing your organization today.
Get the Report →Configure the CData JDBC Driver for Amazon Athena in a Connection Pool in Tomcat
Connect to Amazon Athena data from a connection pool in Tomcat.
The CData JDBC Drivers support standard JDBC interfaces to integrate with Web applications running on the JVM. This article details how to connect to Amazon Athena data from a connection pool in Tomcat.
Connect to Amazon Athena Data through a Connection Pool in Tomcat
- Copy the CData JAR and CData .lic file to $CATALINA_HOME/lib. The CData JAR is located in the lib subfolder of the installation directory.
- Add a definition of the resource to the context. Specify the JDBC URL here.
Authenticating to Amazon Athena
To authorize Amazon Athena requests, provide the credentials for an administrator account or for an IAM user with custom permissions: Set AccessKey to the access key Id. Set SecretKey to the secret access key.
Note: Though you can connect as the AWS account administrator, it is recommended to use IAM user credentials to access AWS services.
Obtaining the Access Key
To obtain the credentials for an IAM user, follow the steps below:
- Sign into the IAM console.
- In the navigation pane, select Users.
- To create or manage the access keys for a user, select the user and then select the Security Credentials tab.
To obtain the credentials for your AWS root account, follow the steps below:
- Sign into the AWS Management console with the credentials for your root account.
- Select your account name or number and select My Security Credentials in the menu that is displayed.
- Click Continue to Security Credentials and expand the Access Keys section to manage or create root account access keys.
Authenticating from an EC2 Instance
If you are using the CData Data Provider for Amazon Athena 2018 from an EC2 Instance and have an IAM Role assigned to the instance, you can use the IAM Role to authenticate. To do so, set UseEC2Roles to true and leave AccessKey and SecretKey empty. The CData Data Provider for Amazon Athena 2018 will automatically obtain your IAM Role credentials and authenticate with them.
Authenticating as an AWS Role
In many situations it may be preferable to use an IAM role for authentication instead of the direct security credentials of an AWS root user. An AWS role may be used instead by specifying the RoleARN. This will cause the CData Data Provider for Amazon Athena 2018 to attempt to retrieve credentials for the specified role. If you are connecting to AWS (instead of already being connected such as on an EC2 instance), you must additionally specify the AccessKey and SecretKey of an IAM user to assume the role for. Roles may not be used when specifying the AccessKey and SecretKey of an AWS root user.
Authenticating with MFA
For users and roles that require Multi-factor Authentication, specify the MFASerialNumber and MFAToken connection properties. This will cause the CData Data Provider for Amazon Athena 2018 to submit the MFA credentials in a request to retrieve temporary authentication credentials. Note that the duration of the temporary credentials may be controlled via the TemporaryTokenDuration (default 3600 seconds).
Connecting to Amazon Athena
In addition to the AccessKey and SecretKey properties, specify Database, S3StagingDirectory and Region. Set Region to the region where your Amazon Athena data is hosted. Set S3StagingDirectory to a folder in S3 where you would like to store the results of queries.
If Database is not set in the connection, the data provider connects to the default database set in Amazon Athena.
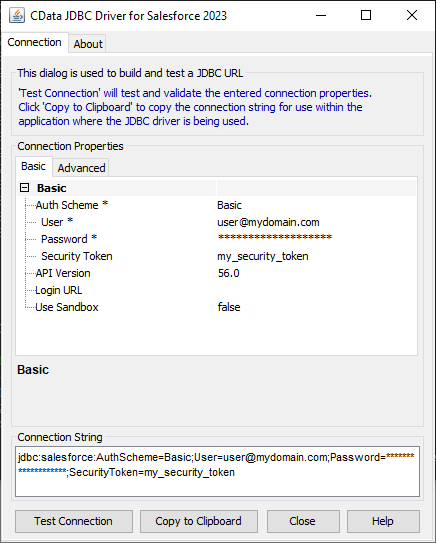
Built-in Connection String Designer
For assistance in constructing the JDBC URL, use the connection string designer built into the Amazon Athena JDBC Driver. Either double-click the JAR file or execute the jar file from the command-line.
java -jar cdata.jdbc.amazonathena.jarFill in the connection properties and copy the connection string to the clipboard.
![Using the built-in connection string designer to generate a JDBC URL (Salesforce is shown.)]()
You can see the JDBC URL specified in the resource definition below.
<Resource name="jdbc/amazonathena" auth="Container" type="javax.sql.DataSource" driverClassName="cdata.jdbc.amazonathena.AmazonAthenaDriver" factory="org.apache.tomcat.jdbc.pool.DataSourceFactory" url="jdbc:amazonathena:AccessKey='a123';SecretKey='s123';Region='IRELAND';Database='sampledb';S3StagingDirectory='s3://bucket/staging/';" maxActive="20" maxIdle="10" maxWait="-1" />To allow a single application to access Amazon Athena data, add the code above to the context.xml in the application's META-INF directory.
For a shared resource configuration, add the code above to the context.xml located in $CATALINA_BASE/conf. A shared resource configuration provides connectivity to Amazon Athena for all applications.
- Add a reference to the resource to the web.xml for the application.
Amazon Athena data JSP jdbc/AmazonAthena javax.sql.DataSource Container -
Initialize connections from the connection pool:
Context initContext = new InitialContext(); Context envContext = (Context)initContext.lookup("java:/comp/env"); DataSource ds = (DataSource)envContext.lookup("jdbc/AmazonAthena"); Connection conn = ds.getConnection();
More Tomcat Integration
The steps above show how to connect to Amazon Athena data in a simple connection pooling scenario. For more use cases and information, see the JNDI Datasource How-To in the Tomcat documentation.