ノーコードでクラウド上のデータとの連携を実現。
詳細はこちら →
CData

こんにちは!ウェブ担当の加藤です。マーケ関連のデータ分析や整備もやっています。
PostgreSQL には多くの対応クライアントがあります。標準のドライバーからBI、アナリティクスツールまで、PostgreSQL はデータ接続の人気のインターフェースです。JDBC ドライバーを使用することで、簡単に任意の標準クライアントから接続できるPostgreSQL エントリポイントを作成できます。
Amazon Athena にPostgreSQL データベースとしてアクセスするには、CData JDBC Driver for AmazonAthena とJDBC foreign data wrapper (FDW) を使用します。この記事ではFDW をコンパイルしてインストールし、PostgreSQL サーバーからAmazon Athena にクエリを実行します。
JDBC データソースとしてAmazon Athena に接続するには、以下が必要です。
Driver クラス
cdata.jdbc.amazonathena.AmazonAthenaDriver
Amazon Athena リクエストの認証には、アカウントの管理のクレデンシャルか、IAM ユーザーのカスタムPermission を設定します。 AccessKey にAccess Key Id、SecretKey にはSecret Access Key を設定します。
AWS アカウントアドミニストレータとしてアクセスできる場合でも、AWS サービスへの接続にはIAM ユーザークレデンシャルを使用することが推奨されます。
IAM ユーザーのクレデンシャル取得は以下のとおり:
AWS ルートアカウントのクレデンシャル取得は以下のとおり:
EC2 インスタンスからCData 製品を使用していて、そのインスタンスにIAM ロールが割り当てられている場合は、認証にIAM ロールを使用できます。 これを行うには、UseEC2Roles をtrue に設定しAccessKey とSecretKey を空のままにします。 CData 製品は自動的にIAM ロールの認証情報を取得し、それらを使って認証します。
多くの場合、認証にはAWS ルートユーザーのダイレクトなセキュリティ認証情報ではなく、IAM ロールを使用することをお勧めします。 代わりにRoleARN を指定してAWS ロールを使用できます。これにより、CData 製品は指定されたロールの資格情報を取得しようと試みます。 (すでにEC2 インスタンスなどで接続されているのではなく)AWS に接続している場合は、役割を担うIAM ユーザーのAccessKeyと SecretKey を追加で指定する必要があります。AWS ルートユーザーのAccessKey およびSecretKey を指定する場合、 ロールは使用できません。
多要素認証を必要とするユーザーおよびロールには、MFASerialNumber およびMFAToken 接続プロパティを指定してください。 これにより、CData 製品は一時的な認証資格情報を取得するために、リクエストでMFA 認証情報を送信します。一時的な認証情報の有効期間 (デフォルトは3600秒)は、TemporaryTokenDuration プロパティを介して制御できます。
AccessKey とSecretKey プロパティに加え、Database、S3StagingDirectory、Region を設定します。Region をAmazon Athena データがホストされているリージョンに設定します。S3StagingDirectory をクエリの結果を格納したいS3内のフォルダに設定します。
接続にDatabase が設定されていない場合は、CData 製品はAmazon Athena に設定されているデフォルトデータベースに接続します。
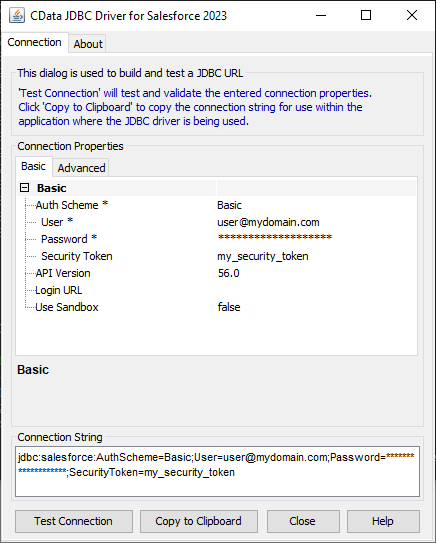
JDBC URL の構成については、Amazon Athena JDBC Driver に組み込まれている接続文字列デザイナを使用できます。JAR ファイルのダブルクリック、またはコマンドラインからJAR ファイルを実行します。
java -jar cdata.jdbc.amazonathena.jar
接続プロパティを入力し、接続文字列をクリップボードにコピーします。
以下は一般的なJDBC URL です。
jdbc:amazonathena:AccessKey='a123';SecretKey='s123';Region='IRELAND';Database='sampledb';S3StagingDirectory='s3://bucket/staging/';
FDW は、PostgreSQL を再コンパイルせずに、PostgreSQL の拡張機能としてインストールできます。例としてjdbc2_fdw 拡張子を使用します。
ln -s /usr/lib/jvm/java-6-openjdk/jre/lib/amd64/server/libjvm.so /usr/lib/libjvm.so
make install USE_PGXS=1
拡張機能をインストールした後、以下のステップに従ってAmazon Athena へのクエリの実行を開始します。
CREATE EXTENSION jdbc2_fdw;
CREATE SERVER AmazonAthena
FOREIGN DATA WRAPPER jdbc2_fdw OPTIONS (
drivername 'cdata.jdbc.amazonathena.AmazonAthenaDriver',
url 'jdbc:amazonathena:AccessKey='a123';SecretKey='s123';Region='IRELAND';Database='sampledb';S3StagingDirectory='s3://bucket/staging/';',
querytimeout '15',
jarfile '/home/MyUser/CData/CData\ JDBC\ Driver\ for\ Salesforce MyDriverEdition/lib/cdata.jdbc.amazonathena.jar');
CREATE USER MAPPING for postgres SERVER AmazonAthena OPTIONS (
username 'admin',
password 'test');
postgres=# CREATE FOREIGN TABLE customers (
customers_id text,
customers_Name text,
customers_TotalDue numeric)
SERVER AmazonAthena OPTIONS (
table_name 'customers');
postgres=# SELECT * FROM customers;
このようにCData JDBC Driver for AmazonAthena を使って簡単にAmazon Athena データを取得して検索対象にすることができました。ぜひ、30日の無償評価版 をお試しください。