Use Agno to Talk to Your SingleStore Data via CData Connect AI
Agno is a developer-first Python framework for building AI agents that reason, plan, and take actions using tools. Agno emphasizes a clean, code-driven architecture where the agent runtime remains fully under developer control.
CData Connect AI provides a secure cloud-to-cloud interface for integrating 300+ enterprise data sources with AI systems. Using Connect AI, live SingleStore data data can be exposed through a remote MCP endpoint without replication.
In this guide, we build a production-ready Agno agent using the Agno Python SDK. The agent connects to CData Connect AI via MCP using streamable HTTP, dynamically discovers available tools, and invokes them to query live SingleStore data.
Prerequisites
- Python 3.9+.
- A CData Connect AI account – Sign up or log in here.
- An active SingleStore account with valid credentials.
- An LLM API key (for example, OpenAI).
Overview
Here is a high-level overview of the process:
- Connect: Configure a SingleStore connection in CData Connect AI.
- Discover: Use MCP to dynamically retrieve tools exposed by CData Connect AI.
- Query: Wrap MCP tools as Agno functions and query live SingleStore data.
Step 1: Configure SingleStore in CData Connect AI
To enable Agno to query live SingleStore data, first create a SingleStore connection in CData Connect AI. This connection is exposed through the CData Remote MCP Server.
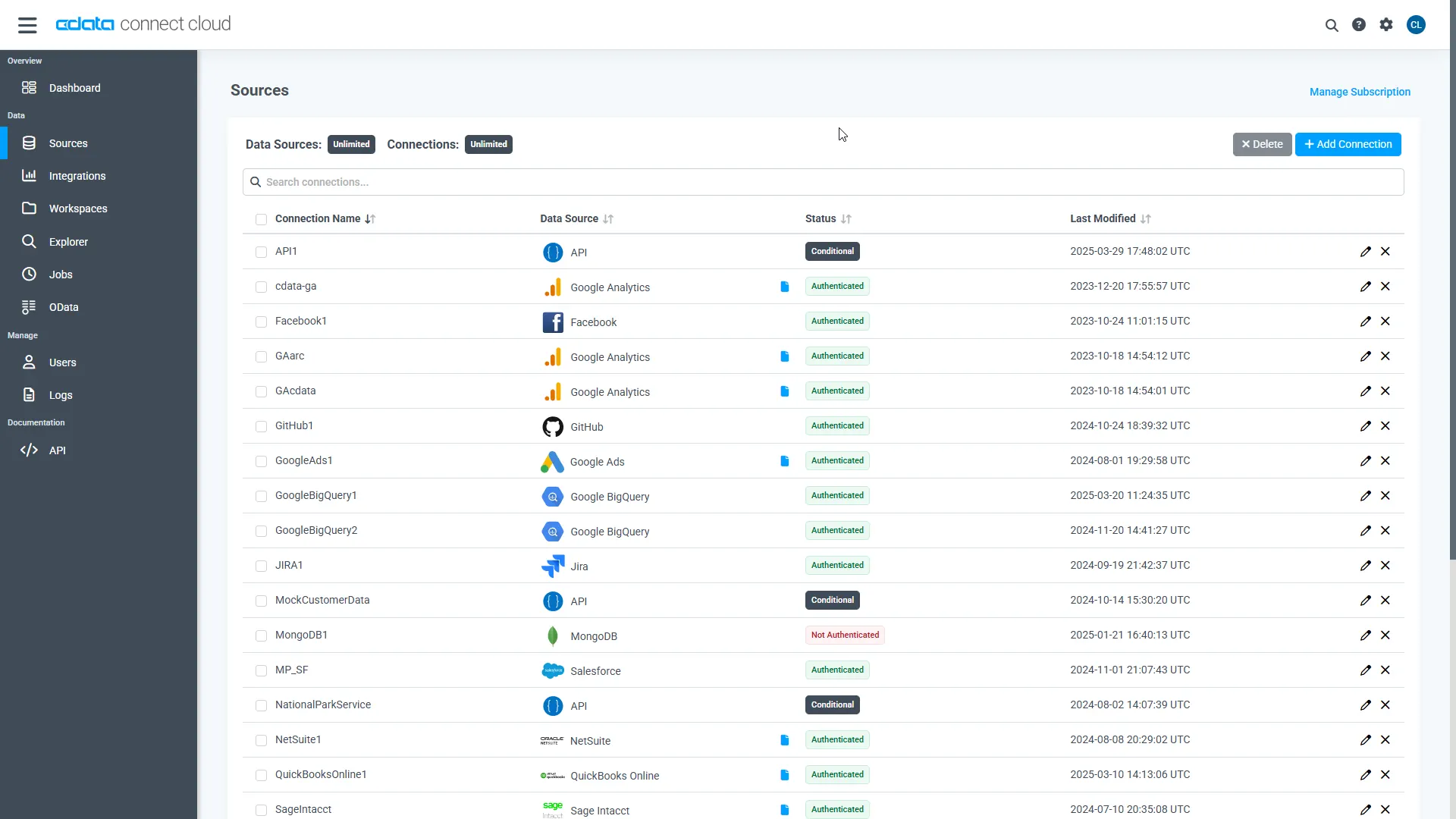
-
Log into Connect AI, click Sources, and then click
Add Connection.
-
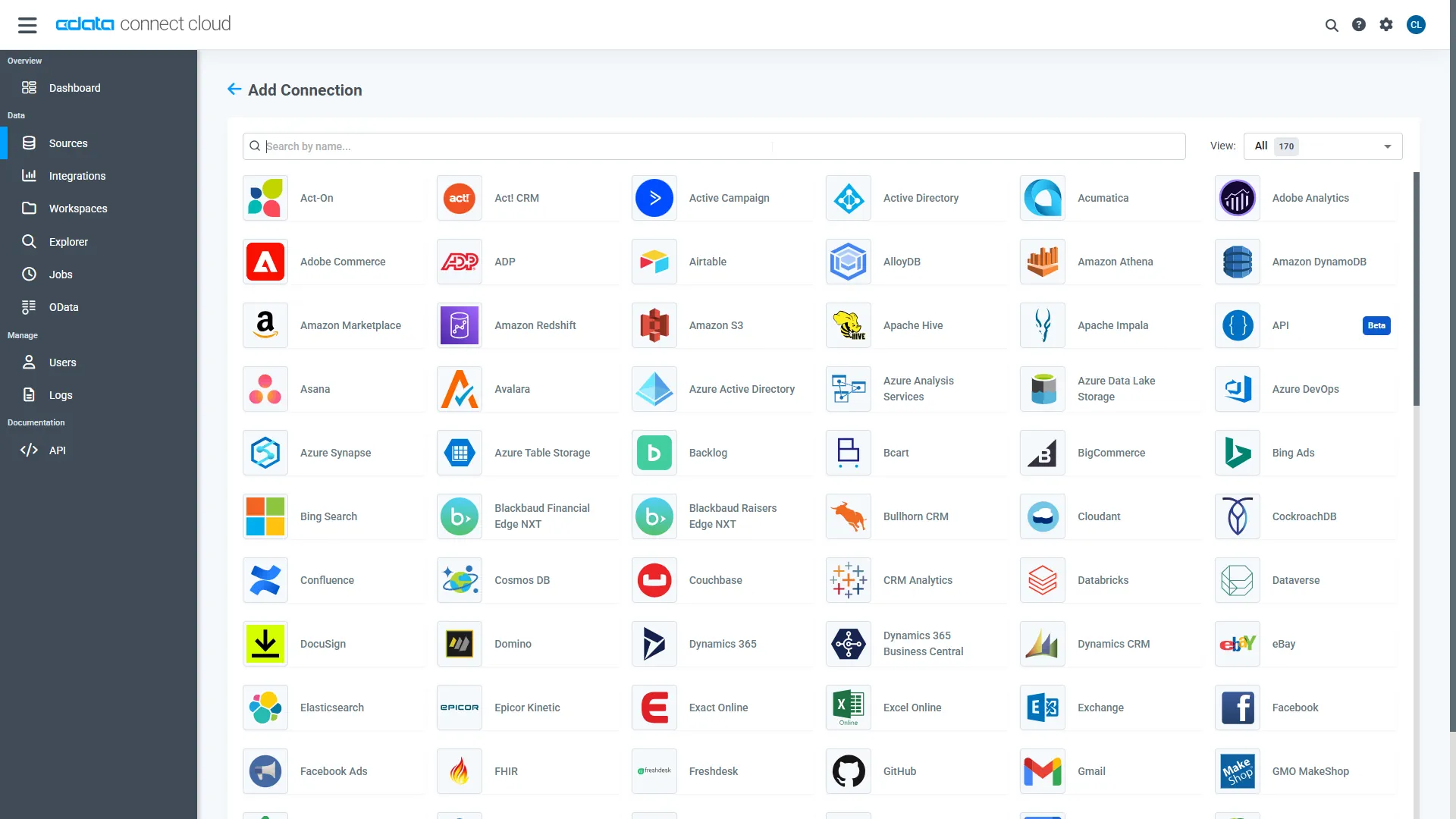
Select "SingleStore" from the Add Connection panel.
-
Enter the required authentication properties.
The following connection properties are required in order to connect to data.
- Server: The host name or IP of the server hosting the SingleStore database.
- Port: The port of the server hosting the SingleStore database.
- Database (Optional): The default database to connect to when connecting to the SingleStore Server. If this is not set, tables from all databases will be returned.
Connect Using Standard Authentication
To authenticate using standard authentication, set the following:
- User: The user which will be used to authenticate with the SingleStore server.
- Password: The password which will be used to authenticate with the SingleStore server.
Connect Using Integrated Security
As an alternative to providing the standard username and password, you can set IntegratedSecurity to True to authenticate trusted users to the server via Windows Authentication.
Connect Using SSL Authentication
You can leverage SSL authentication to connect to SingleStore data via a secure session. Configure the following connection properties to connect to data:
- SSLClientCert: Set this to the name of the certificate store for the client certificate. Used in the case of 2-way SSL, where truststore and keystore are kept on both the client and server machines.
- SSLClientCertPassword: If a client certificate store is password-protected, set this value to the store's password.
- SSLClientCertSubject: The subject of the TLS/SSL client certificate. Used to locate the certificate in the store.
- SSLClientCertType: The certificate type of the client store.
- SSLServerCert: The certificate to be accepted from the server.
Connect Using SSH Authentication
Using SSH, you can securely login to a remote machine. To access SingleStore data via SSH, configure the following connection properties:
- SSHClientCert: Set this to the name of the certificate store for the client certificate.
- SSHClientCertPassword: If a client certificate store is password-protected, set this value to the store's password.
- SSHClientCertSubject: The subject of the TLS/SSL client certificate. Used to locate the certificate in the store.
- SSHClientCertType: The certificate type of the client store.
- SSHPassword: The password that you use to authenticate with the SSH server.
- SSHPort: The port used for SSH operations.
- SSHServer: The SSH authentication server you are trying to authenticate against.
- SSHServerFingerPrint: The SSH Server fingerprint used for verification of the host you are connecting to.
- SSHUser: Set this to the username that you use to authenticate with the SSH server.
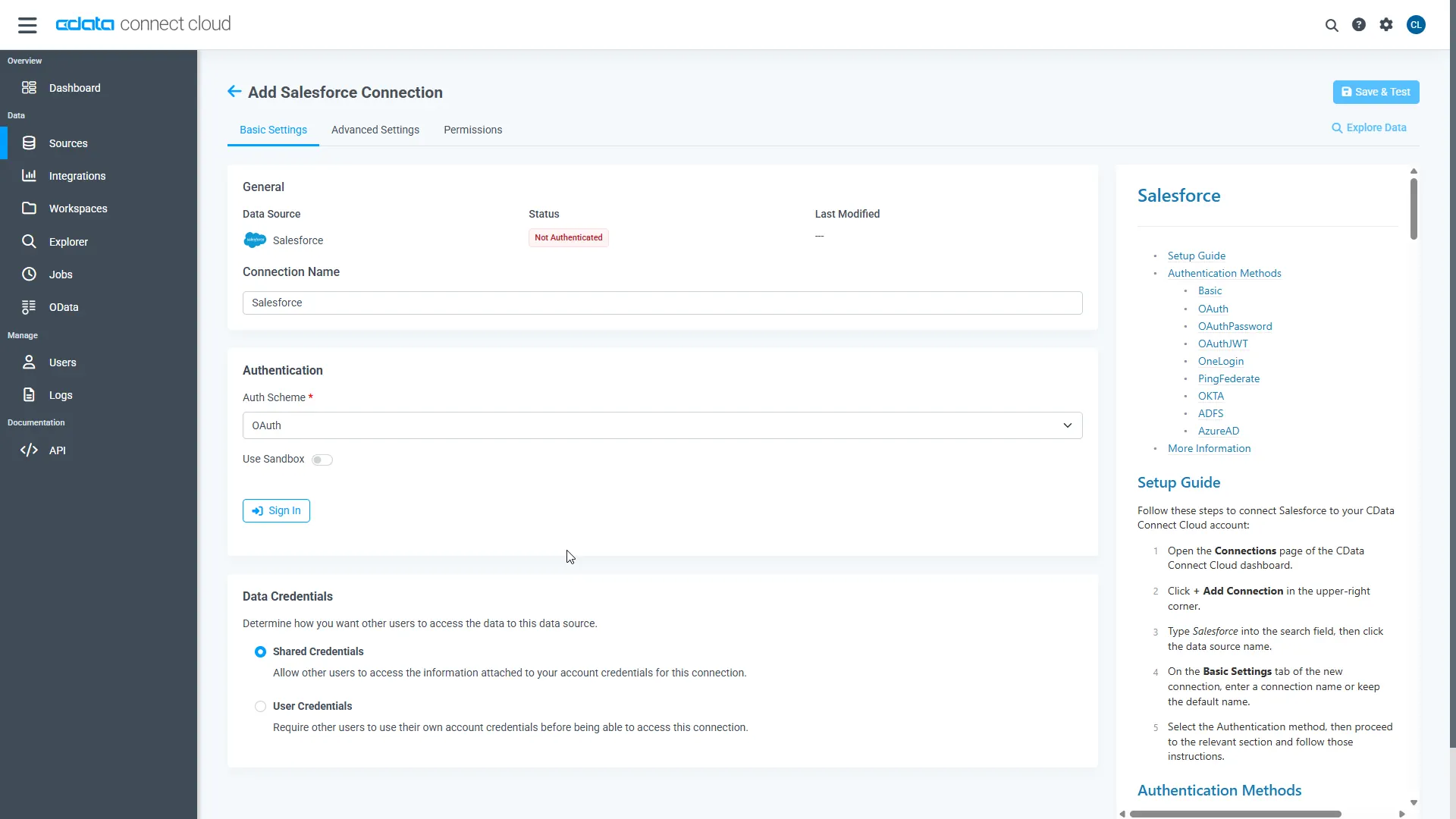 Click Create & Test.
Click Create & Test.
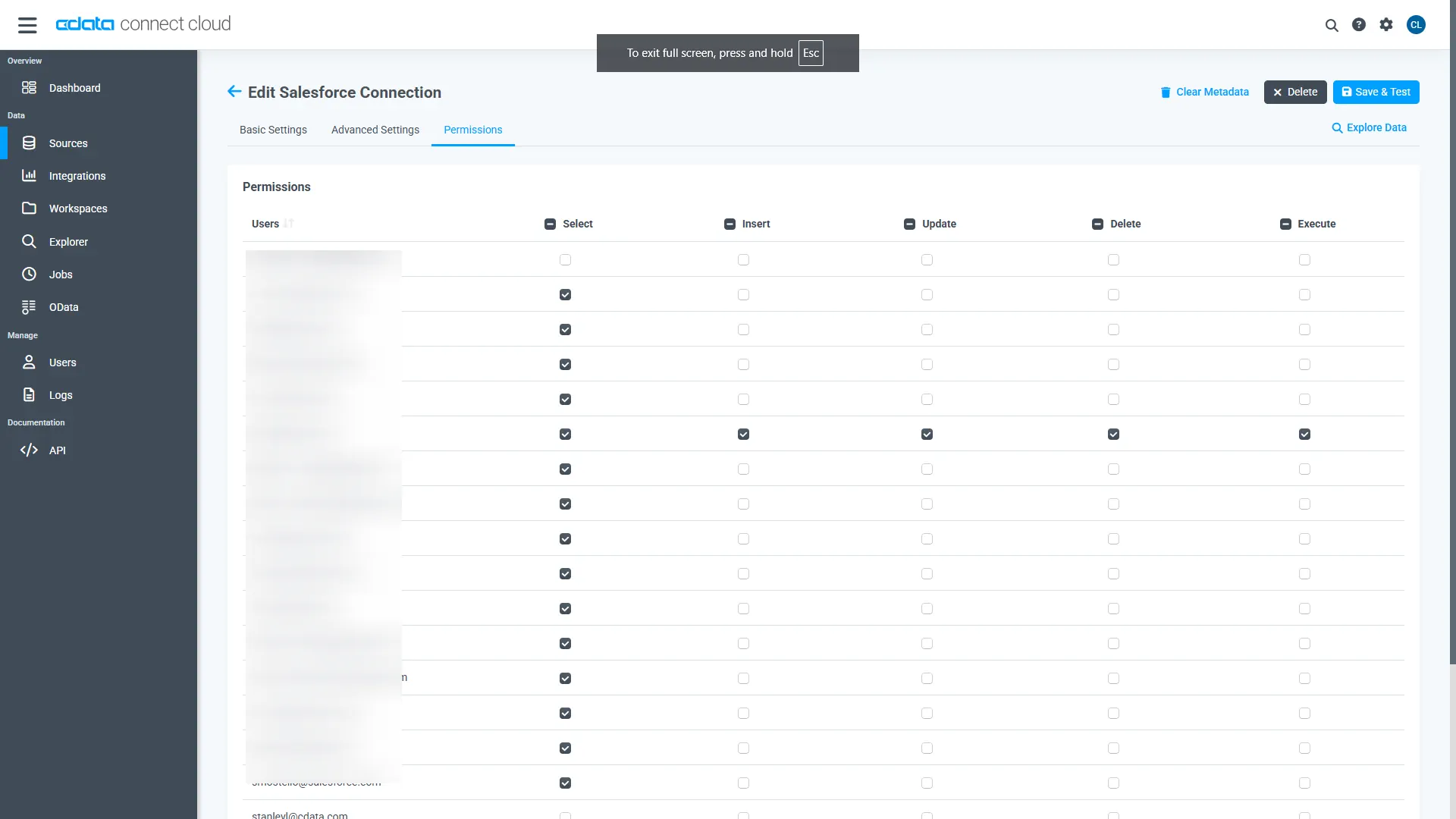
-
Open the Permissions tab and configure user access.
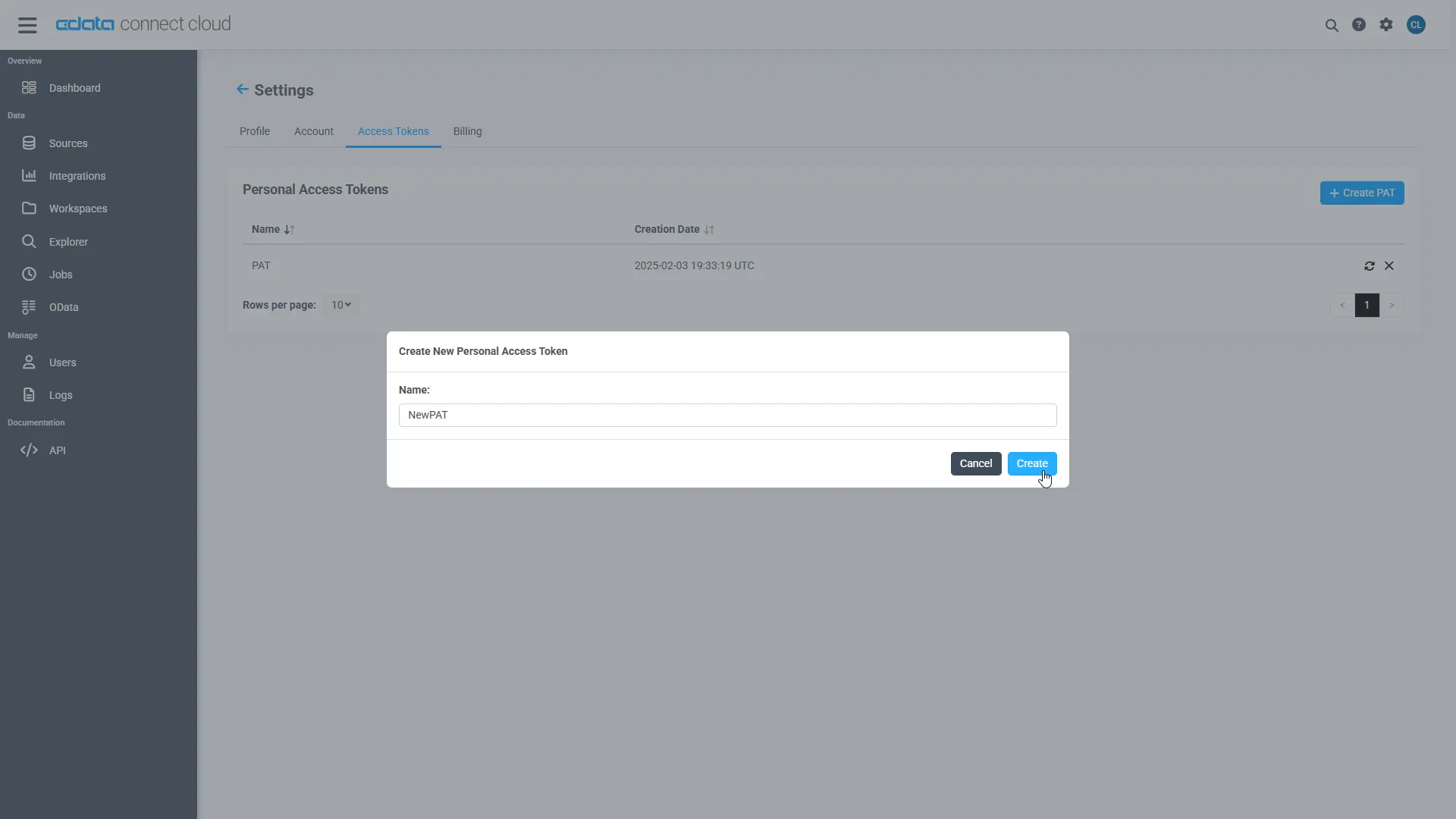
Add a Personal Access Token
A Personal Access Token (PAT) authenticates MCP requests from Agno to CData Connect AI.
- Open Settings and navigate to Access Tokens.
- Click Create PAT.
-
Save the generated token securely.
Step 2: Install dependencies and configure environment variables
Install Agno and the MCP adapter dependencies. LangChain is included strictly for MCP tool compatibility.
pip install agno agno-mcp langchain-mcp-adapters
Configure environment variables:
export CDATA_MCP_URL="https://mcp.cloud.cdata.com/mcp" export CDATA_MCP_AUTH="Base64EncodedCredentials" export OPENAI_API_KEY="your-openai-key"
Where "Base64EncodedCredentials" is your Connect AI user email and your Personal Access Token joined by a colon (":") and Base64 Encoded: Base64([email protected]:MY_CONNECT_AI_PAT)
Step 3: Connect to CData Connect AI via MCP
Create an MCP client using streamable HTTP. This establishes a secure connection to CData Connect AI.
import os
from langchain_mcp_adapters.client import MultiServerMCPClient
mcp_client = MultiServerMCPClient(
connections={
"default": {
"transport": "streamable_http",
"url": os.environ["CDATA_MCP_URL"],
"headers": {
"Authorization": f"Basic {os.environ['CDATA_MCP_AUTH']}"
}
}
}
)
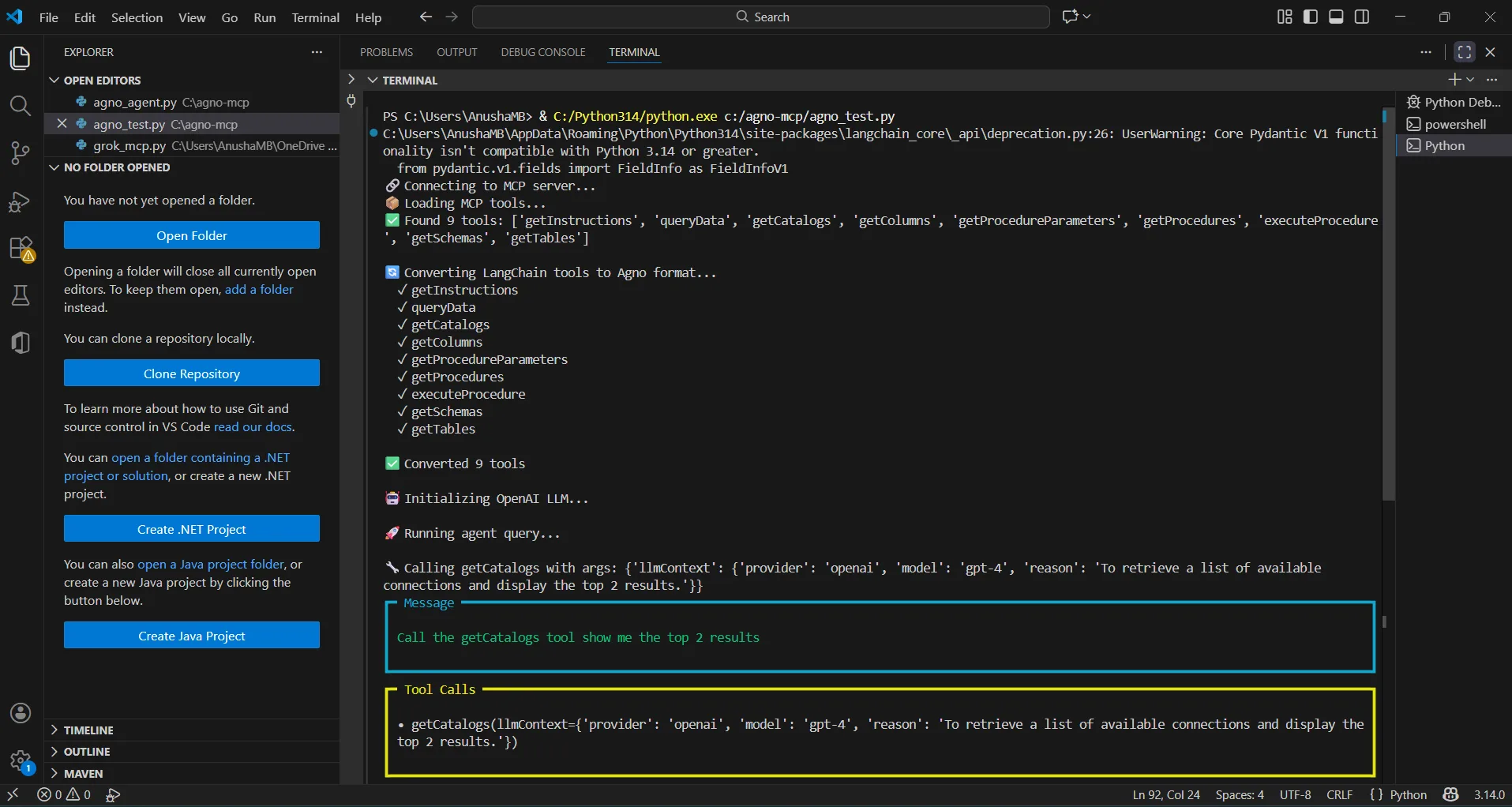
Step 4: Discover MCP tools
CData Connect AI exposes operations as MCP tools. These are retrieved dynamically at runtime.
langchain_tools = await mcp_client.get_tools() for tool in langchain_tools: print(tool.name)
Step 5: Convert MCP tools to Agno functions
Each MCP tool is wrapped as an Agno function so it can be used by the agent.
NOTE: Agno performs all reasoning, planning, and tool selection.LangChain is used only as a lightweight MCP compatibility layer to consume tools exposed by CData Connect AI.
from agno.tools import Function
def make_tool_caller(lc_tool):
async def call_tool(**kwargs):
return await lc_tool.ainvoke(kwargs)
return call_tool
Step 6: Create an Agno agent and query live SingleStore data
Agno performs all reasoning, planning, and tool invocation. LangChain plays no role beyond MCP compatibility.
from agno.agent import Agent
from agno.models.openai import OpenAIChat
agent = Agent(
model=OpenAIChat(
id="gpt-4o",
temperature=0.2,
api_key=os.environ["OPENAI_API_KEY"]
),
tools=agno_tools,
markdown=True
)
await agent.aprint_response(
"Show me the top 5 records from the available data source"
)
if __name__ == "__main__":
asyncio.run(main())
The results below show an Agno agent invoking MCP tools through CData Connect AI and returning live SingleStore data data.
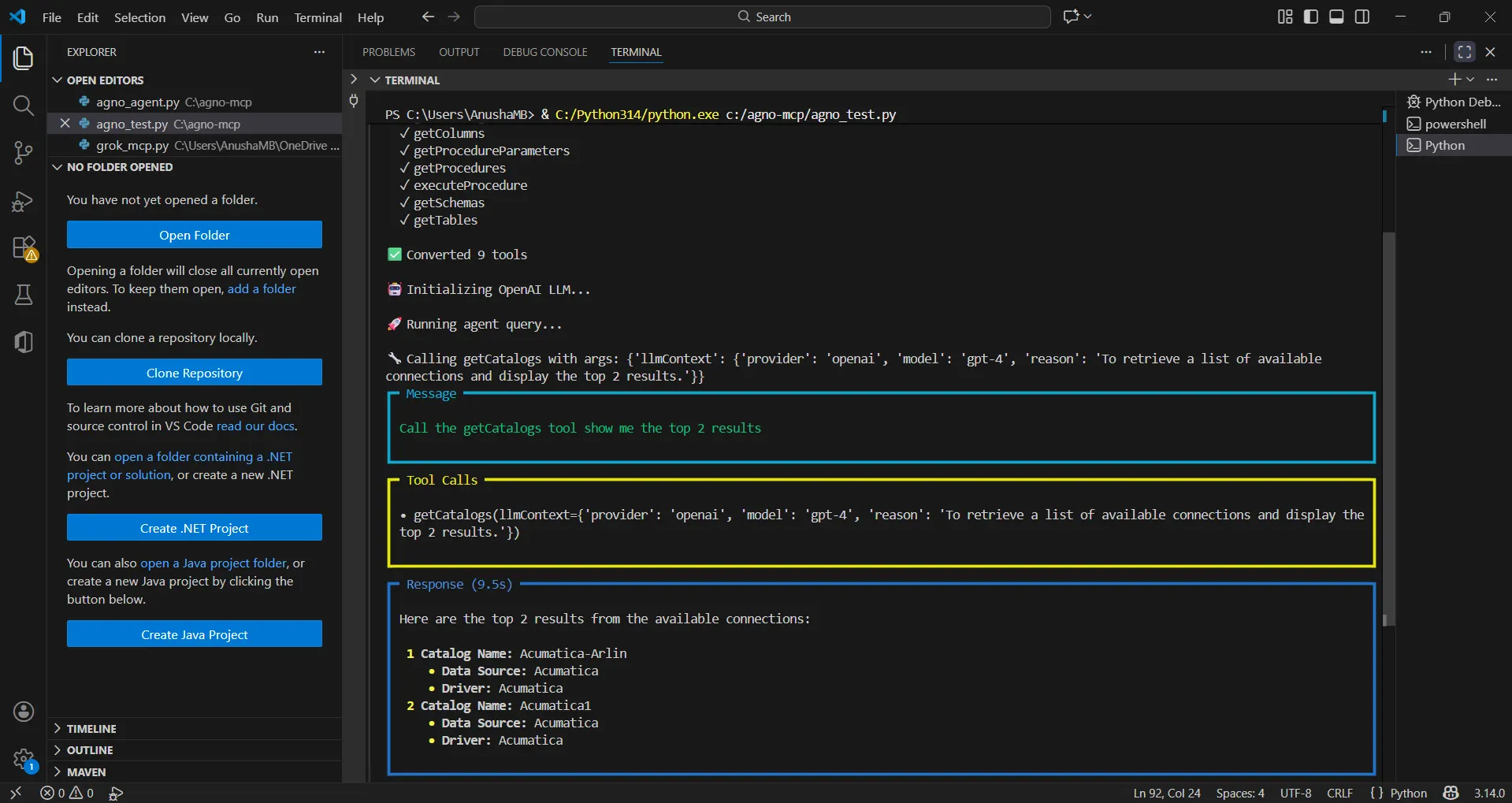
You can now query live SingleStore data using natural language through your Agno agent.
Get CData Connect AI
To get live data access to 300+ SaaS, Big Data, and NoSQL sources directly from your cloud applications, try CData Connect AI today!





