Access Live SingleStore Data in Emergent via CData Connect AI
Emergent is an AI-powered development platform that lets users describe what they want to build and have an autonomous agent generate full-stack web applications in real time. Agents can connect to external tools and data sources through MCP to retrieve live data and power their outputs.
By integrating Emergent with CData Connect AI through the built-in MCP (Model Context Protocol) Server, Emergent agents gain governed, real-time access to live SingleStore data. This enables agents to query, analyze, and visualize SingleStore data: either by calling MCP tools directly during a session, or by generating a full application wired to live data, all without manual data exports or custom integration code.
This article outlines the steps to configure SingleStore connectivity in Connect AI, register the CData MCP Server in Emergent, and interact with live SingleStore data from Emergent.
Step 1: Configure SingleStore connectivity for Emergent
Connectivity to SingleStore from Emergent is made possible through CData Connect AI's Remote MCP Server. To interact with SingleStore data from Emergent, start by creating and configuring a SingleStore connection in CData Connect AI.
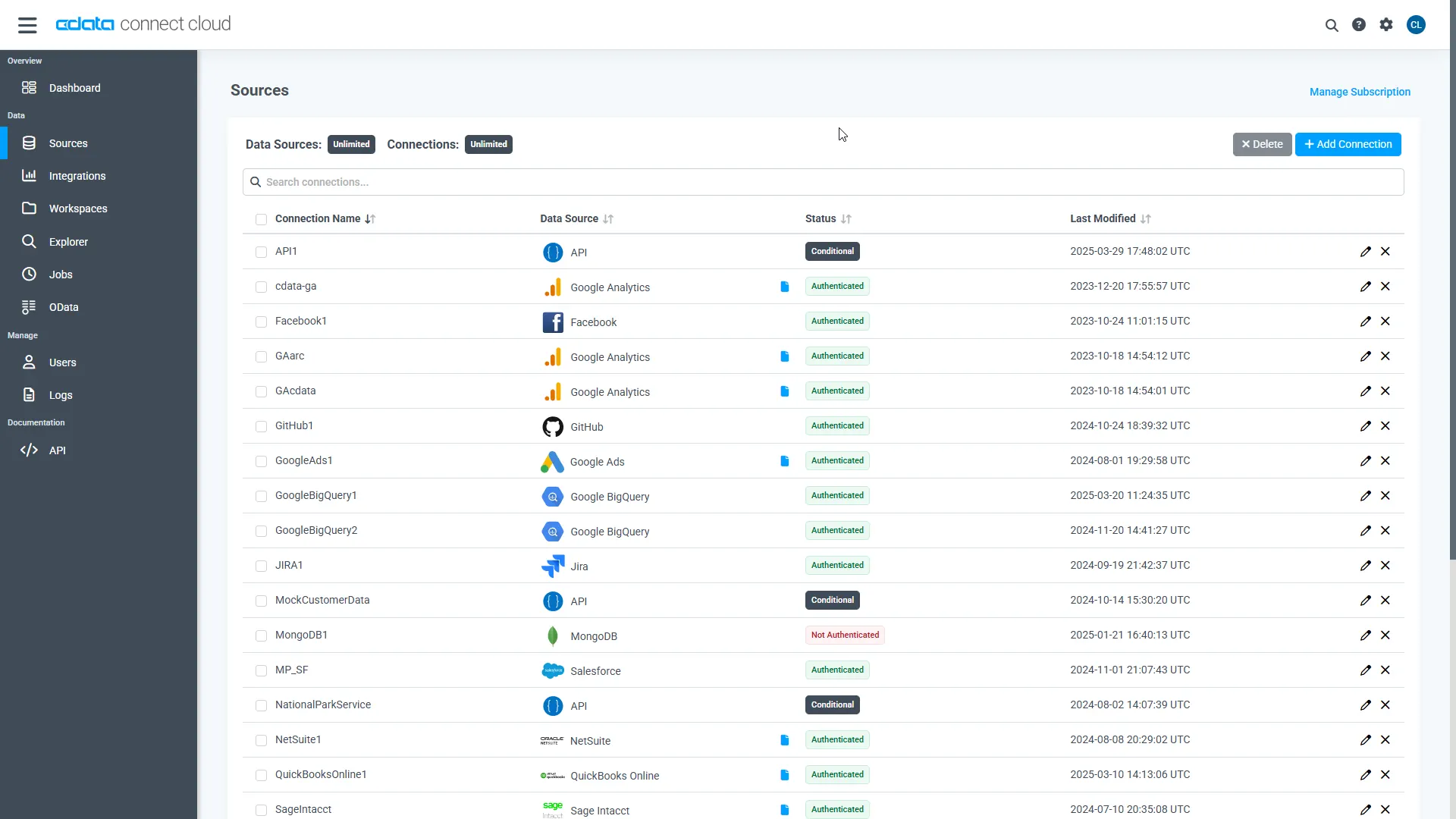
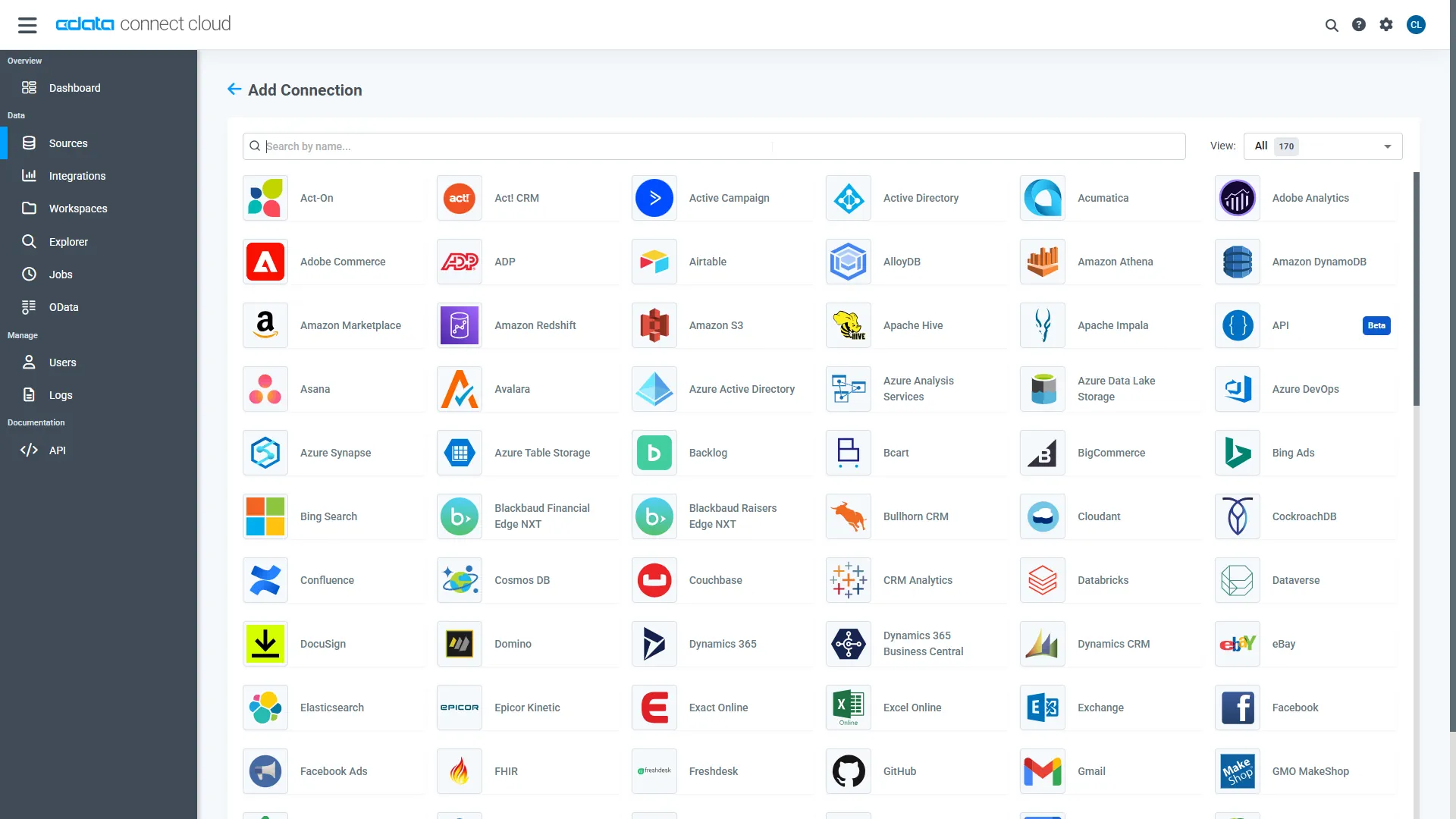
- Log into Connect AI, click Sources, and then click Add Connection
- Select SingleStore from the Add Connection panel
-
Enter the necessary authentication properties to connect to SingleStore.
The following connection properties are required in order to connect to data.
- Server: The host name or IP of the server hosting the SingleStore database.
- Port: The port of the server hosting the SingleStore database.
- Database (Optional): The default database to connect to when connecting to the SingleStore Server. If this is not set, tables from all databases will be returned.
Connect Using Standard Authentication
To authenticate using standard authentication, set the following:
- User: The user which will be used to authenticate with the SingleStore server.
- Password: The password which will be used to authenticate with the SingleStore server.
Connect Using Integrated Security
As an alternative to providing the standard username and password, you can set IntegratedSecurity to True to authenticate trusted users to the server via Windows Authentication.
Connect Using SSL Authentication
You can leverage SSL authentication to connect to SingleStore data via a secure session. Configure the following connection properties to connect to data:
- SSLClientCert: Set this to the name of the certificate store for the client certificate. Used in the case of 2-way SSL, where truststore and keystore are kept on both the client and server machines.
- SSLClientCertPassword: If a client certificate store is password-protected, set this value to the store's password.
- SSLClientCertSubject: The subject of the TLS/SSL client certificate. Used to locate the certificate in the store.
- SSLClientCertType: The certificate type of the client store.
- SSLServerCert: The certificate to be accepted from the server.
Connect Using SSH Authentication
Using SSH, you can securely login to a remote machine. To access SingleStore data via SSH, configure the following connection properties:
- SSHClientCert: Set this to the name of the certificate store for the client certificate.
- SSHClientCertPassword: If a client certificate store is password-protected, set this value to the store's password.
- SSHClientCertSubject: The subject of the TLS/SSL client certificate. Used to locate the certificate in the store.
- SSHClientCertType: The certificate type of the client store.
- SSHPassword: The password that you use to authenticate with the SSH server.
- SSHPort: The port used for SSH operations.
- SSHServer: The SSH authentication server you are trying to authenticate against.
- SSHServerFingerPrint: The SSH Server fingerprint used for verification of the host you are connecting to.
- SSHUser: Set this to the username that you use to authenticate with the SSH server.
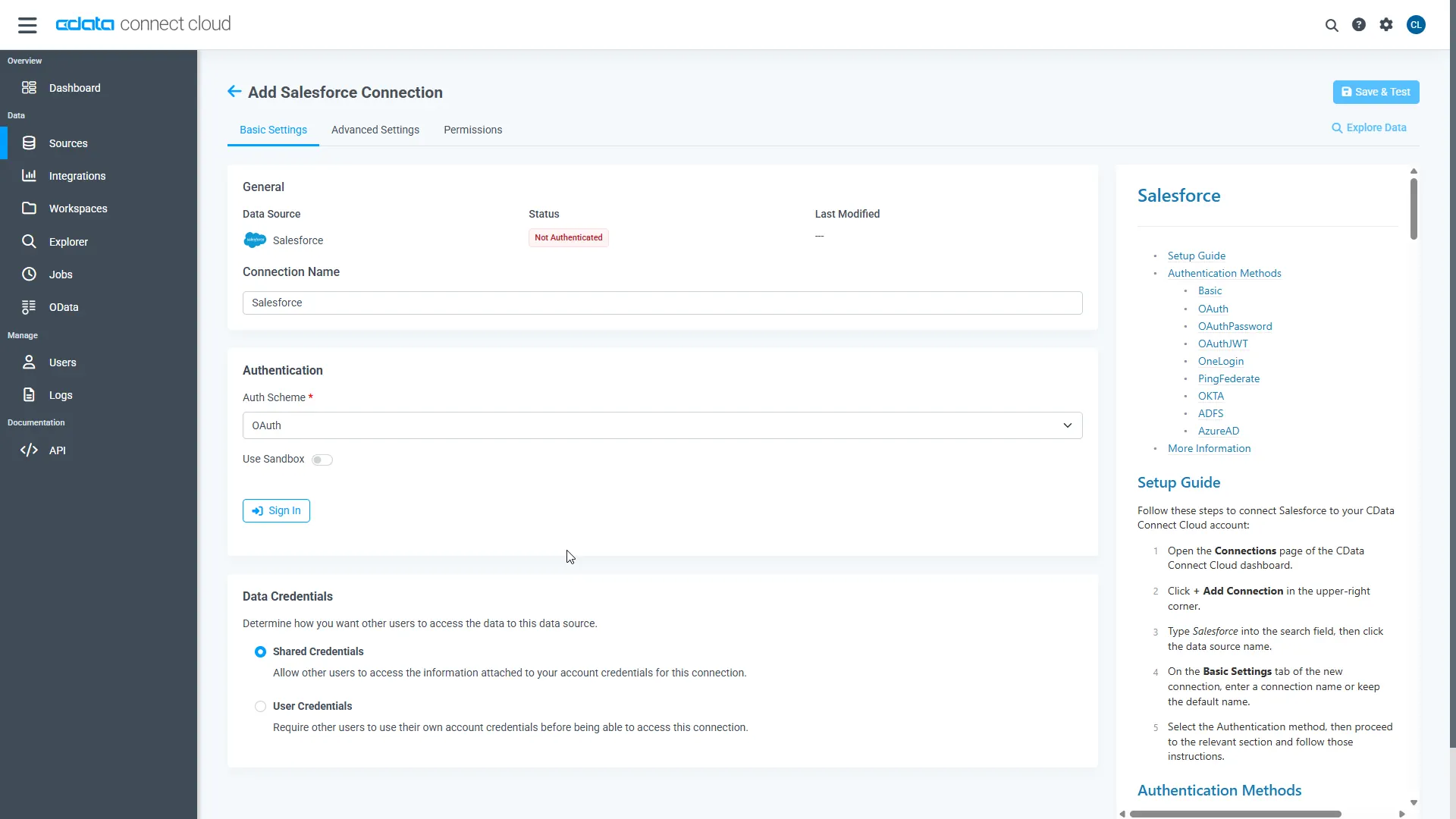
- Click Save & Test
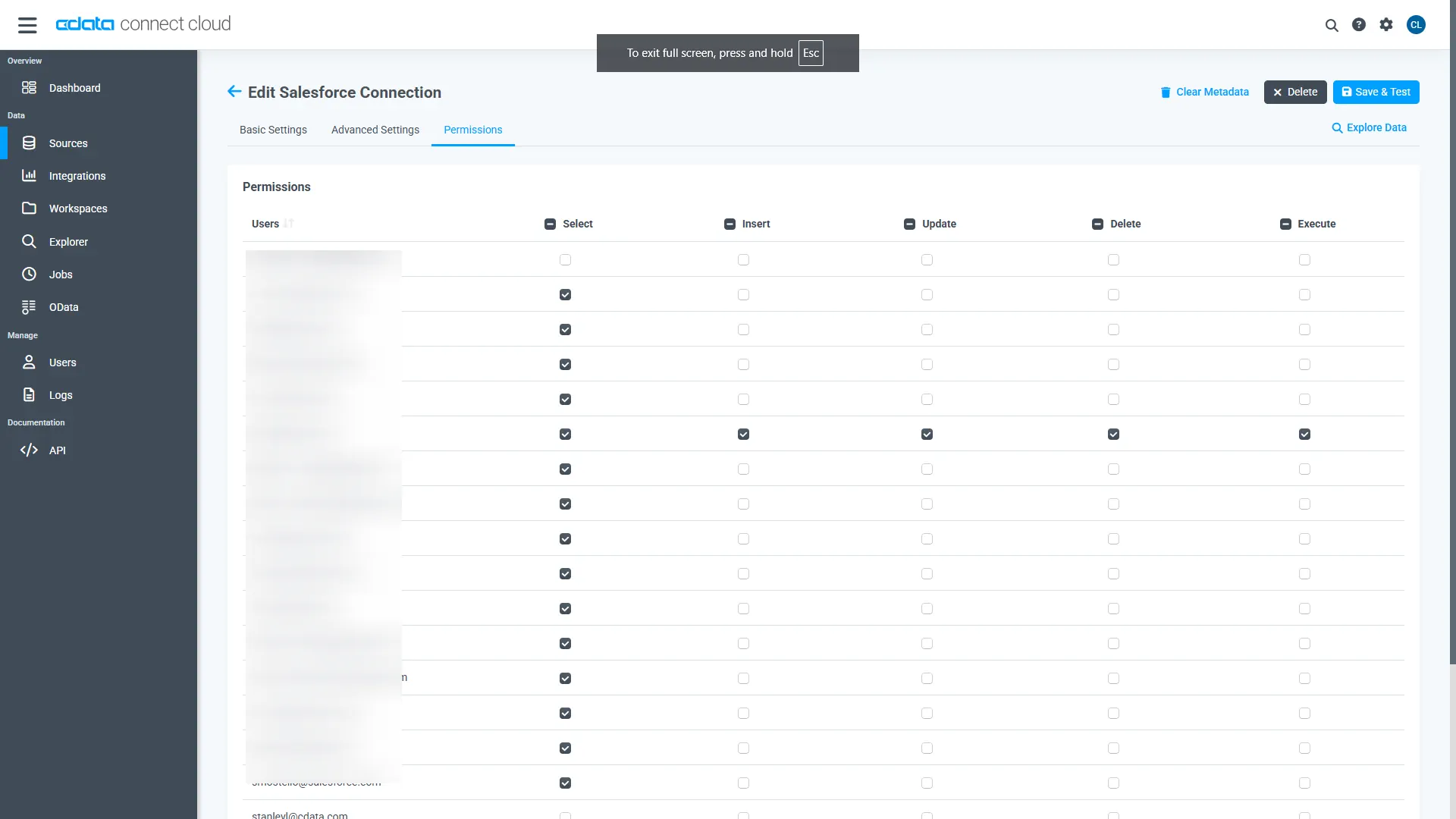
- Navigate to the Permissions tab and update user-based permissions
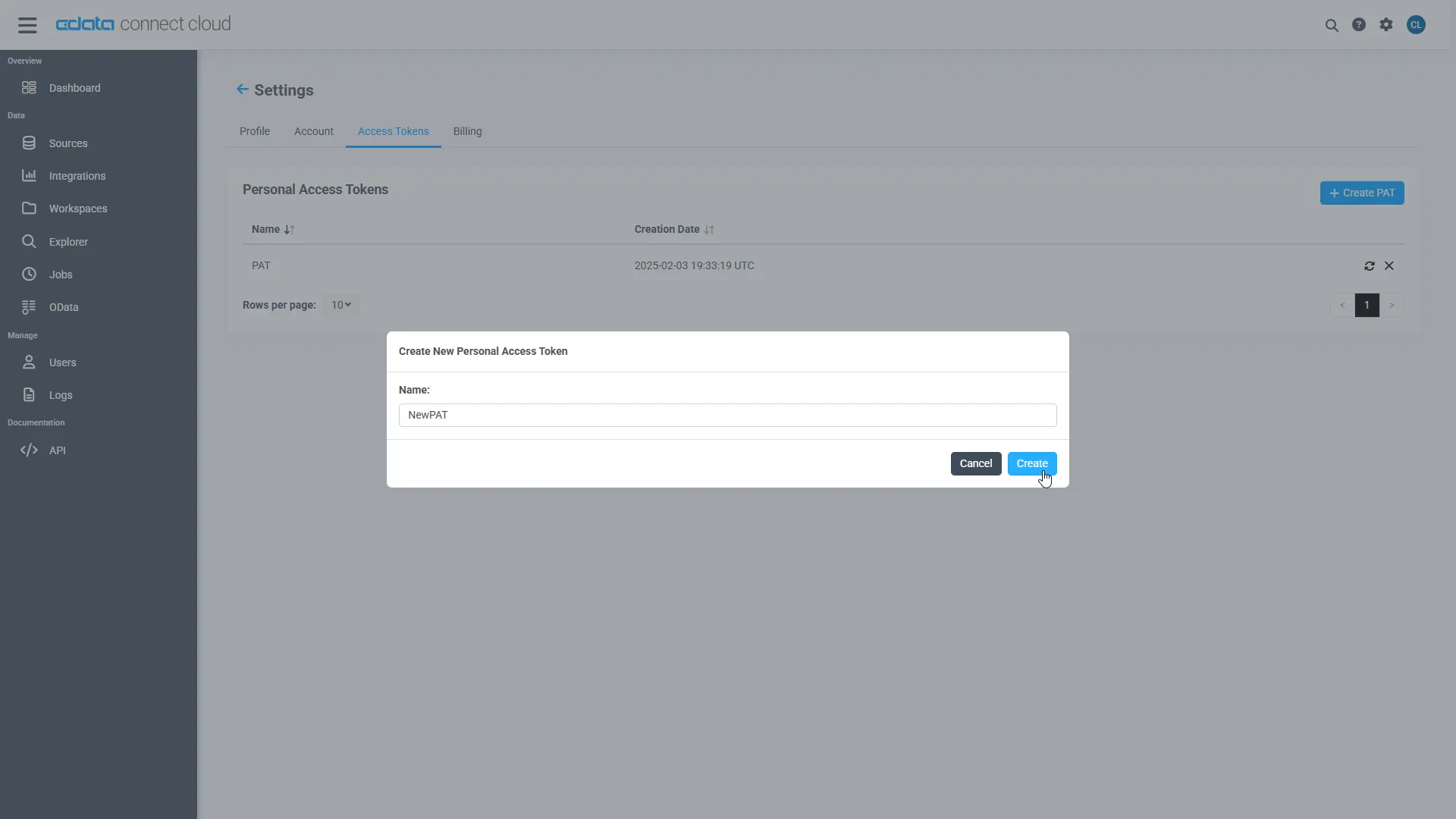
Add a Personal Access Token
A Personal Access Token (PAT) is used to authenticate the connection to Connect AI from Emergent. It is best practice to create a separate PAT for each integration to maintain granular access control.
- Click the gear icon () at the top right of the Connect AI app to open Settings
- On the Settings page, go to the Access Tokens section and click Create PAT
- Give the PAT a descriptive name and click Create
- Copy the token when displayed and store it securely. It will not be shown again
With the SingleStore connection configured and a PAT generated, Emergent can now connect to SingleStore data through Connect AI.
Step 2: Configure Connect AI in Emergent
CData Connect AI can be integrated with Emergent in two ways depending on your account tier. Pro and Enterprise users can register the MCP Server directly in the Emergent UI, while free-tier users can describe the integration in natural language and have Emergent's agent build a connected application automatically.
Method 1: Direct MCP Configuration (Pro/Enterprise)
Pro and Enterprise users can register the CData Connect AI MCP Server directly in the Emergent UI. Once registered, agents in any project can call live SingleStore data through MCP tools without additional setup.
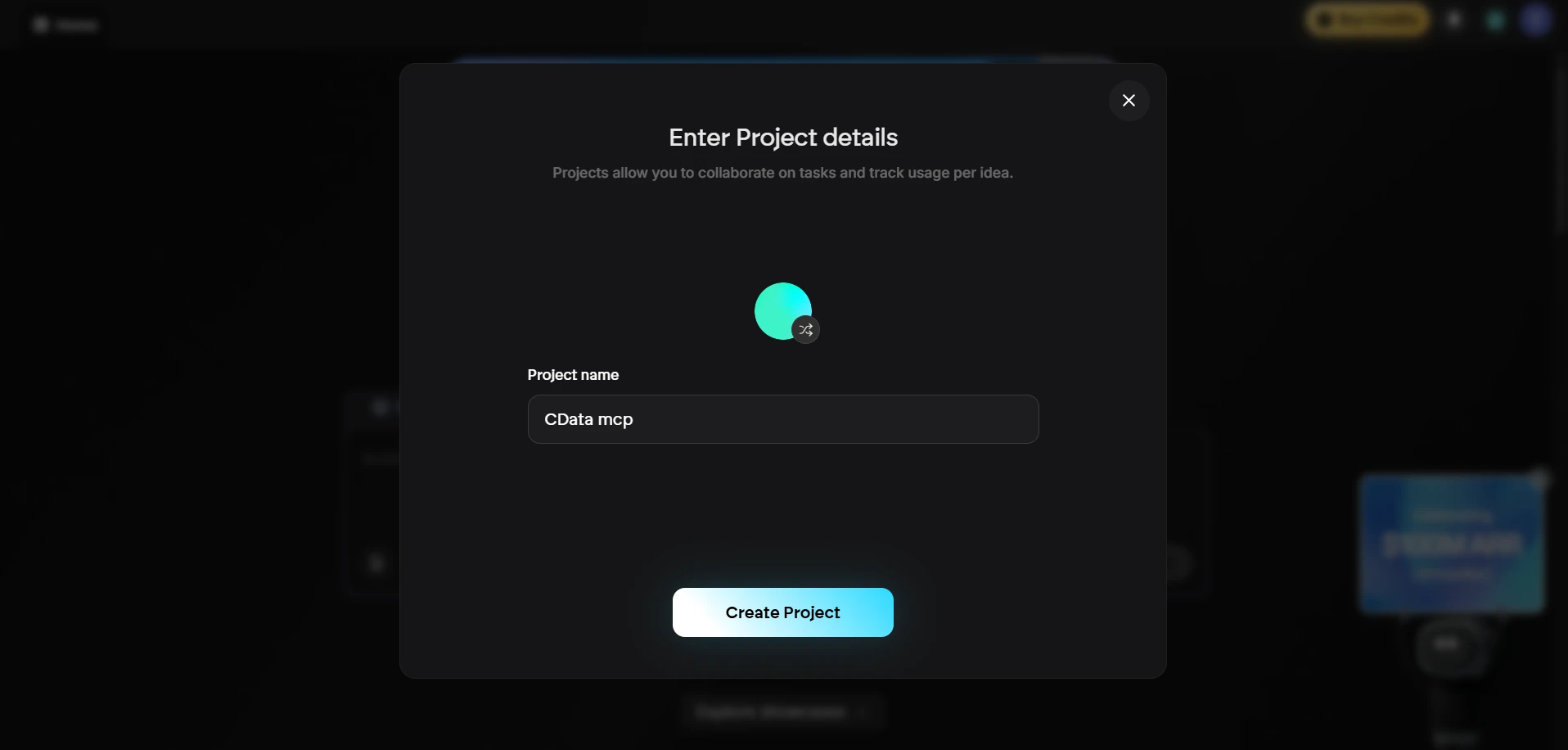
- Sign in to Emergent and create an account if you do not already have one
-
Click to start a new project. Enter a Project Name and click Create Project
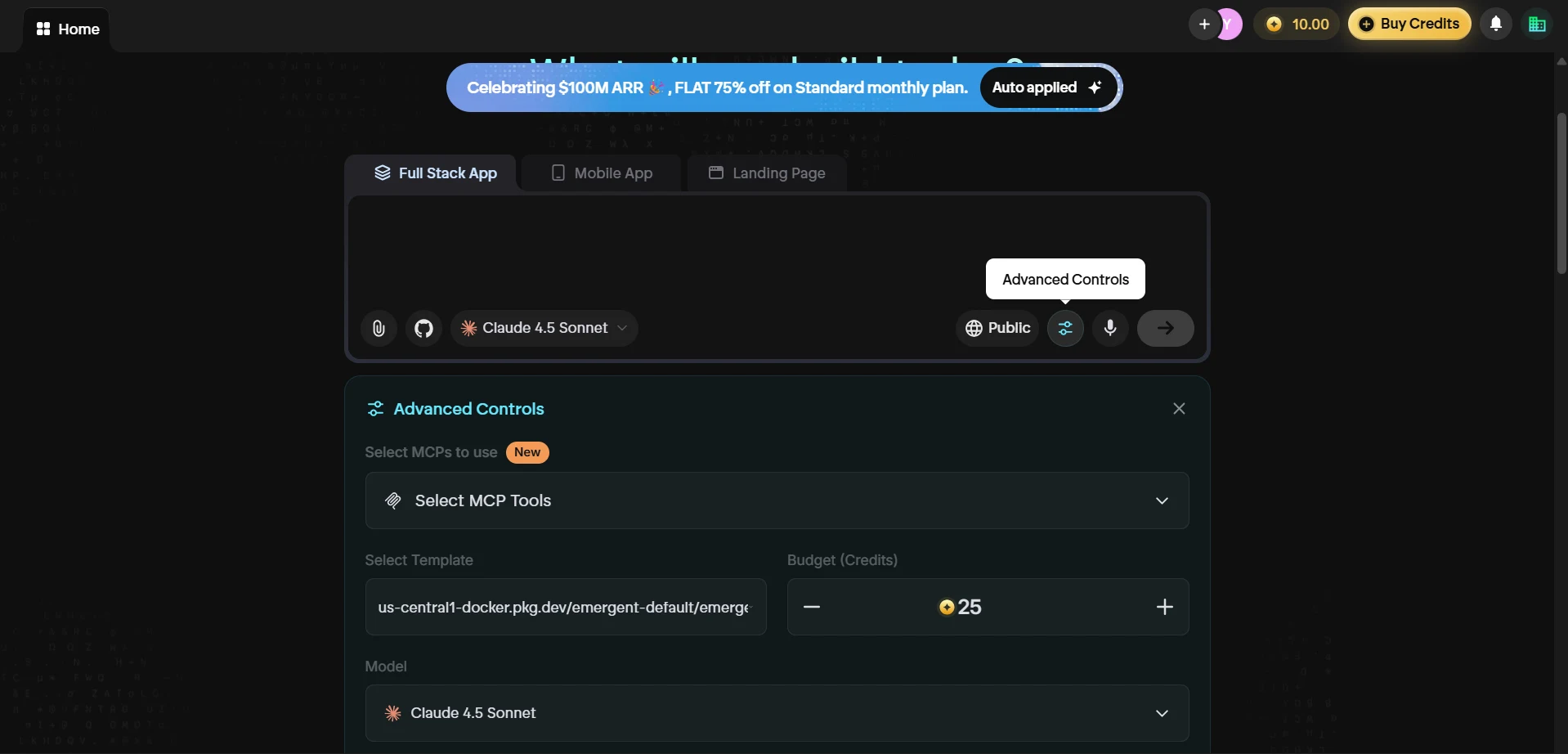
- In the project chat window, select your preferred model from the dropdown (e.g., Claude 4.5 Sonnet)
-
Click the Advanced Controls icon and then click Select MCP Tools to open the MCP configuration panel
-
In the Select MCPs to use dialog, click + New MCP Server to add a custom MCP server
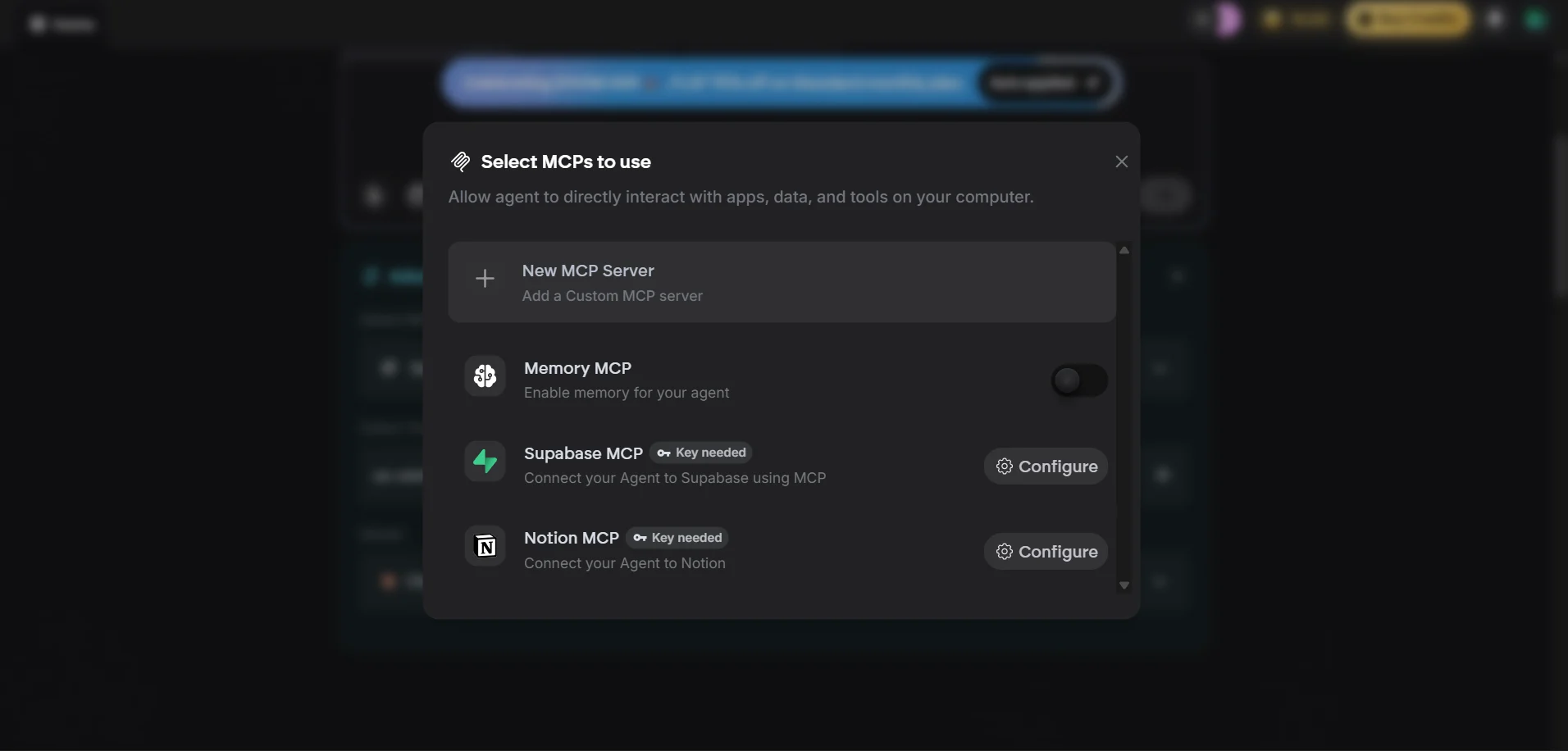
-
In the Configure New MCP dialog, fill in the following:
- MCP Name: cdata-mcp
- Description: (optional) A brief description of the server
- JSON Configuration: Paste the following, replacing base64-encode-email-pat with your Base64-encoded email:PAT string:
{ "mcpServers": { "cdata-mcp": { "args": [ "-y", "mcp-client", "connect", "https://mcp.cloud.cdata.com/mcp" ], "command": "npx", "env": { "MCP_HEADERS": "{\"Authorization\":\"Basic base64-encode-email-pat\"}" } } } }Note: Combine your Connect AI email and PAT in the format email:PAT, then Base64 encode the combined string. For example, given [email protected]:ABC123...XYZ, the value becomes something like: dXNlckBteWRvbWFpbjphSzkvbVB4Mi9Rcjd2TjQ...
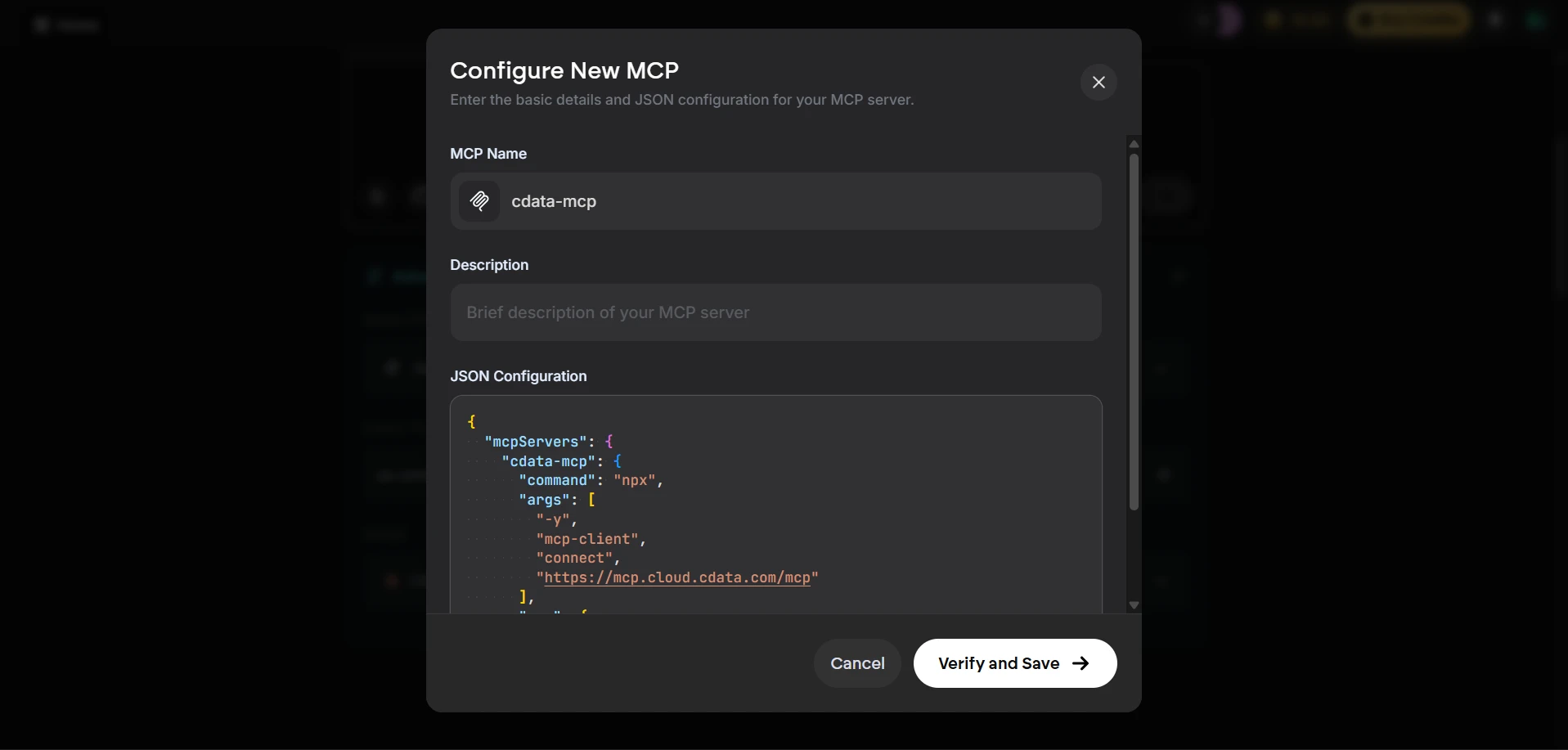
- Click Verify and Save to register the MCP server
- Return to Select MCP Tools and confirm that cdata-mcp is listed and its toggle is enabled. If it is not enabled, toggle it on
With the CData MCP Server registered and enabled, Emergent agents can now query and act on live SingleStore data through Connect AI in any project.
Query live SingleStore data from Emergent
With the MCP server configured, start a conversation in the Emergent agent panel to interact with live SingleStore data.
-
Return to the project chat and enter a prompt to explore your data, for example:
- List all available catalogs in my cdata-mcp connection.
- Show the schemas and tables available for SingleStore.
- Query the top 5 records from SingleStore data.
- The agent calls the CData Connect AI MCP Server and returns live results from SingleStore data
Method 2: Build an application with natural language (Free)
Free-tier users can direct Emergent to build a full-stack application that connects to the CData Connect AI MCP Server through a natural language prompt. The agent will gather the required endpoint and credentials interactively, then generate a working application wired to live SingleStore data.
- Sign in to Emergent and open the chat window
-
Enter a prompt that describes the application you want to build. For example:
I would like to build a small application that connects to a remote MCP HTTPS server. I already have the MCP endpoint URL and the required credentials. The application should: - Establish a connection to the remote MCP server - Authenticate using the provided credentials - Retrieve and list all available catalogs from the MCP Please make sure the credentials are stored securely in a .env file and not hardcoded in the application. -
Emergent will prompt you to provide the MCP endpoint URL and authentication credentials. Supply the following values:
- MCP Endpoint URL: https://mcp.cloud.cdata.com/mcp
- Authorization: Basic base64(email:PAT)
-
The Emergent agent generates a full-stack application that connects to SingleStore data through Connect AI and renders live results in the App Preview panel.
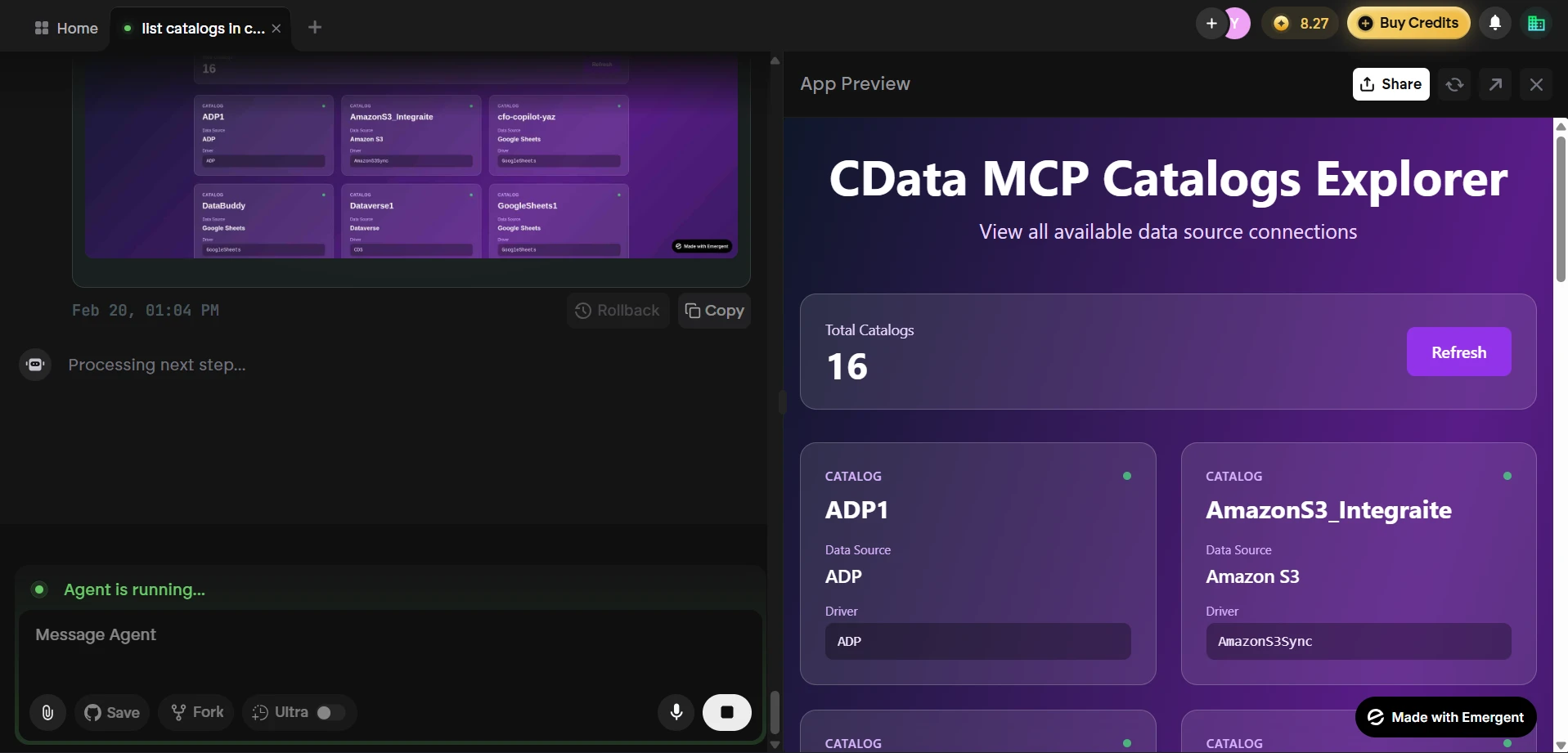
At this point, Emergent has built an application that communicates with the CData Connect AI MCP Server and retrieves live SingleStore data, all from a single natural language prompt.
Get CData Connect AI
To access 350+ SaaS, Big Data, and NoSQL sources directly from your cloud applications, try CData Connect AI today! Sign up for a free 14-day trial of CData Connect AI, and as always, our world-class Support Team is available to assist you with any questions you may have.






