Discover how a bimodal integration strategy can address the major data management challenges facing your organization today.
Get the Report →Connect to Amazon Athena Data in DigitalSuite Studio through RunMyProcess DSEC
Use Arkobi Digital's low-code cloud native platform RunMyProcess's DigitalSuite EnterpriseConnect (DSEC) to connect to Amazon Athena.
The CData JDBC Driver for Amazon Athena implements JDBC Standards and enables a applications ranging from BI to IDE to connect with Amazon Athena. In this article, we describe how to connect to Amazon Athena data from Arkobi Digital RunMyProcess's DSEC and connect to Amazon Athena in RunMyProcess.
Setting up EnterpriseConnect Agent
Configure the EnterpriseConnect Agent following the EnterpriseConnect page in the RunMyProcess documentation.
Setting up JDBC Adapter
The JDBC Adapter section describes the steps to connect to RDBMS through JDBC. Follow the steps and open the JDBC.config file.
- Create a JSON entry for the CData JDBC Driver for Amazon Athena, e.g.
AmazonAthena = { "sqlDriver" : "...", "sqlSource" : "...", "sqlDriverPath" : "..." } - Set the "sqlDriver" field to the Class name for the CData JDBC Driver, e.g.
cdata.jdbc.amazonathena.AmazonAthenaDriver - Set the "sqlSource" field to a JDBC URL for connecting to Amazon Athena, e.g.
jdbc:amazonathena:AccessKey='a123';SecretKey='s123';Region='IRELAND';Database='sampledb';S3StagingDirectory='s3://bucket/staging/';Built-in Connection String Designer
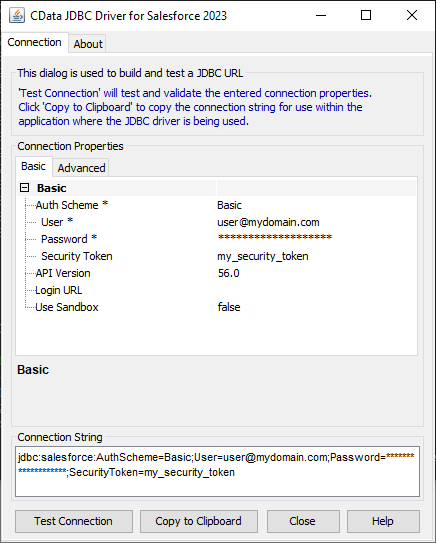
For assistance in constructing the JDBC URL, use the connection string designer built into the Amazon Athena JDBC Driver. Either double-click the JAR file or execute the jar file from the command-line.
java -jar cdata.jdbc.amazonathena.jarFill in the connection properties and copy the connection string to the clipboard.
Authenticating to Amazon Athena
To authorize Amazon Athena requests, provide the credentials for an administrator account or for an IAM user with custom permissions: Set AccessKey to the access key Id. Set SecretKey to the secret access key.
Note: Though you can connect as the AWS account administrator, it is recommended to use IAM user credentials to access AWS services.
Obtaining the Access Key
To obtain the credentials for an IAM user, follow the steps below:
- Sign into the IAM console.
- In the navigation pane, select Users.
- To create or manage the access keys for a user, select the user and then select the Security Credentials tab.
To obtain the credentials for your AWS root account, follow the steps below:
- Sign into the AWS Management console with the credentials for your root account.
- Select your account name or number and select My Security Credentials in the menu that is displayed.
- Click Continue to Security Credentials and expand the Access Keys section to manage or create root account access keys.
Authenticating from an EC2 Instance
If you are using the CData Data Provider for Amazon Athena 2018 from an EC2 Instance and have an IAM Role assigned to the instance, you can use the IAM Role to authenticate. To do so, set UseEC2Roles to true and leave AccessKey and SecretKey empty. The CData Data Provider for Amazon Athena 2018 will automatically obtain your IAM Role credentials and authenticate with them.
Authenticating as an AWS Role
In many situations it may be preferable to use an IAM role for authentication instead of the direct security credentials of an AWS root user. An AWS role may be used instead by specifying the RoleARN. This will cause the CData Data Provider for Amazon Athena 2018 to attempt to retrieve credentials for the specified role. If you are connecting to AWS (instead of already being connected such as on an EC2 instance), you must additionally specify the AccessKey and SecretKey of an IAM user to assume the role for. Roles may not be used when specifying the AccessKey and SecretKey of an AWS root user.
Authenticating with MFA
For users and roles that require Multi-factor Authentication, specify the MFASerialNumber and MFAToken connection properties. This will cause the CData Data Provider for Amazon Athena 2018 to submit the MFA credentials in a request to retrieve temporary authentication credentials. Note that the duration of the temporary credentials may be controlled via the TemporaryTokenDuration (default 3600 seconds).
Connecting to Amazon Athena
In addition to the AccessKey and SecretKey properties, specify Database, S3StagingDirectory and Region. Set Region to the region where your Amazon Athena data is hosted. Set S3StagingDirectory to a folder in S3 where you would like to store the results of queries.
If Database is not set in the connection, the data provider connects to the default database set in Amazon Athena.
![Using the built-in connection string designer to generate a JDBC URL (Salesforce is shown.)]()
- Set the "sqlDriverPath" field to the name of the CData JDBC Driver JAR file, e.g.
cdata.jdbc.amazonathena.jar
Sample JDBC.config File
#DBAgent Configuration
AmazonAthena = {"sqlDriver" : "cdata.jdbc.amazonathena.AmazonAthenaDriver", "sqlSource" = "jdbc:amazonathena:AccessKey='a123';SecretKey='s123';Region='IRELAND';Database='sampledb';S3StagingDirectory='s3://bucket/staging/';","sqlDriverPath" = "cdata.jdbc.amazonathena.jar" }
Put the JDBC driver JAR file (cdata.jdbc.amazonathena.jar) into the same directory as unified-adapter-[version].jar.
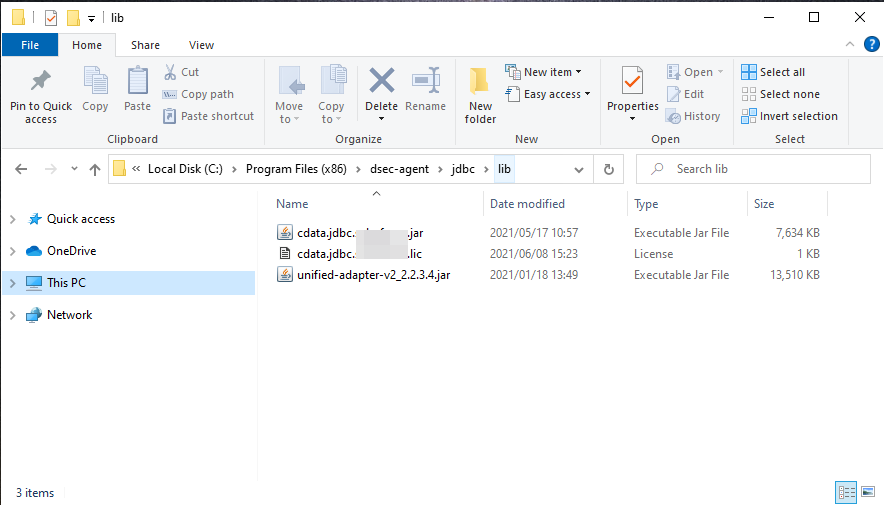
Note: Make sure to put the CData license file (cdata.jdbc.amazonathena.lic) into the same directory. Since the license is generated based on the unique identifier of the machine where the product in installed, you will need an offline activation if you want to put the file on another machine.
Starting DigitalSuite EnterpriseConnect Agent
In Windows, start RunMyProcess DigitalSuite EnterpriseConnect Agent in Windows services. To start the application through command line, see Starting the EnterpriseConnect Agent in the RunMyProcess documents.
Starting the JDBC Adapter
Start the JDBC Adapter from runAdapter.bat. Once the Adapter is running, you can access the application through the agent address (e.g. 127.0.0.1:8080). Below is an example executing the command in Windows.
... > java -Djava.util.logging.config.file=./log.properties -cp lib/* org.runmyprocess.sec2.AdapterHandler :
2021-06-09 14:37:58|INFO|correlationId=|Searching for config file...
2021-06-09 14:37:58|INFO|correlationId=|Adapter Handler started with [JDBC] configuration
2021-06-09 14:37:59|INFO|correlationId=|agent address: 127.0.0.1:8080
2021-06-09 14:38:00.251:INFO::ConnectionThread: Logging initialized @1820ms to org.eclipse.jetty.util.log.StdErrLog
2021-06-09 14:38:00|INFO|correlationId=|onConnect() websocket connection between Agent and Adapter established
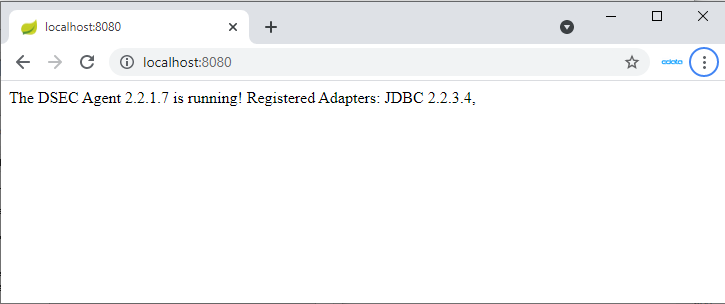
Once the DigitalSuite EnterpriseConnect Agent and JDBC Adapter are running, access http://localhost:(specified-port-number)/ through your browser to open the page shown below.
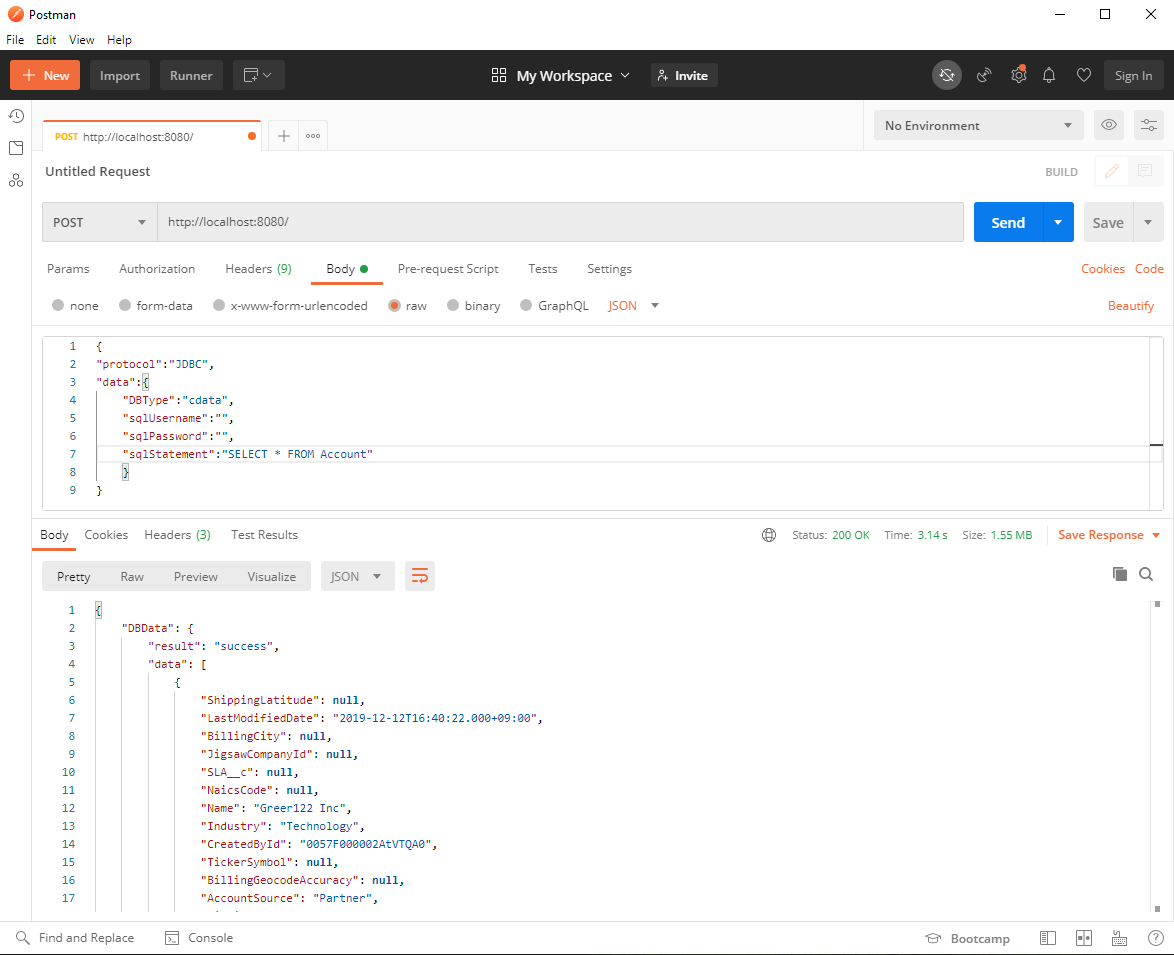
Check the availability of the JDBC Adapter using tools such as Postman or cURL. Here, we use Postman to send the HTTP POST request.
Configure the RequestHeader as follows:
Content-Type application/json
Configure the RequestBody as follows:
{
"protocol":"JDBC",
"data":{
"DBType":"AmazonAthena",
"sqlUsername":"",
"sqlPassword":"",
"sqlStatement":"SELECT * FROM Customers"
}
}
If the JDBC.config file contains credential information, sqlUsername and sqlPassword can be left empty. If you are not sure of the table name, you can retrieve the list of tables using the request SELECT * FROM sys_tables
The request is successful if the Status is 200 and the Body contains Amazon Athena data in JSON format.
Connect to Amazon Athena through DSEC Agent in DigitalSuite Studio
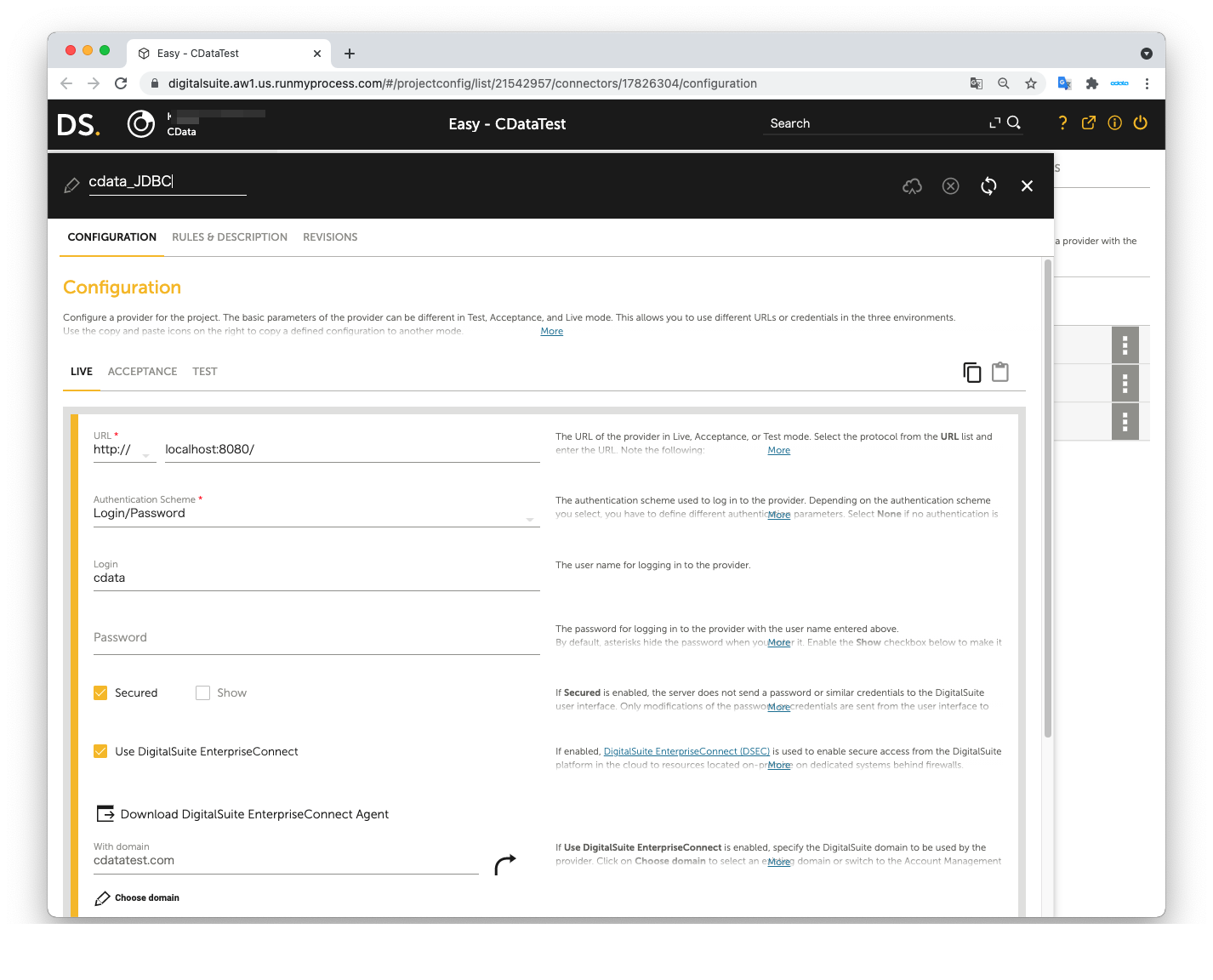
Create a DigitalSuite Studio project and then create a Provider in the project.
- URL: The URL for accessing JDBC Agent (e.g. http:localhost:8080/)
- Authentication Scheme: Login/password
- Login: The value from agent.user in the application.properties file
- Password: agent.password in the application.properties file
- Secured: Checked
- Use DigitalSuite EnterpriseConnect: Checked
- With domain: The value from agent.domain in application.properties file
Next, create a Connector in the Provider.
- Connector URL: Leave this empty
- Architecture: REST/XML-RPC
- Method: POST
- Result format: JSON
- Accept media type: application/json
- Character set: Automatic
- Content: Same as the Request body used in the JDBC Adapter
- Content type: application/json
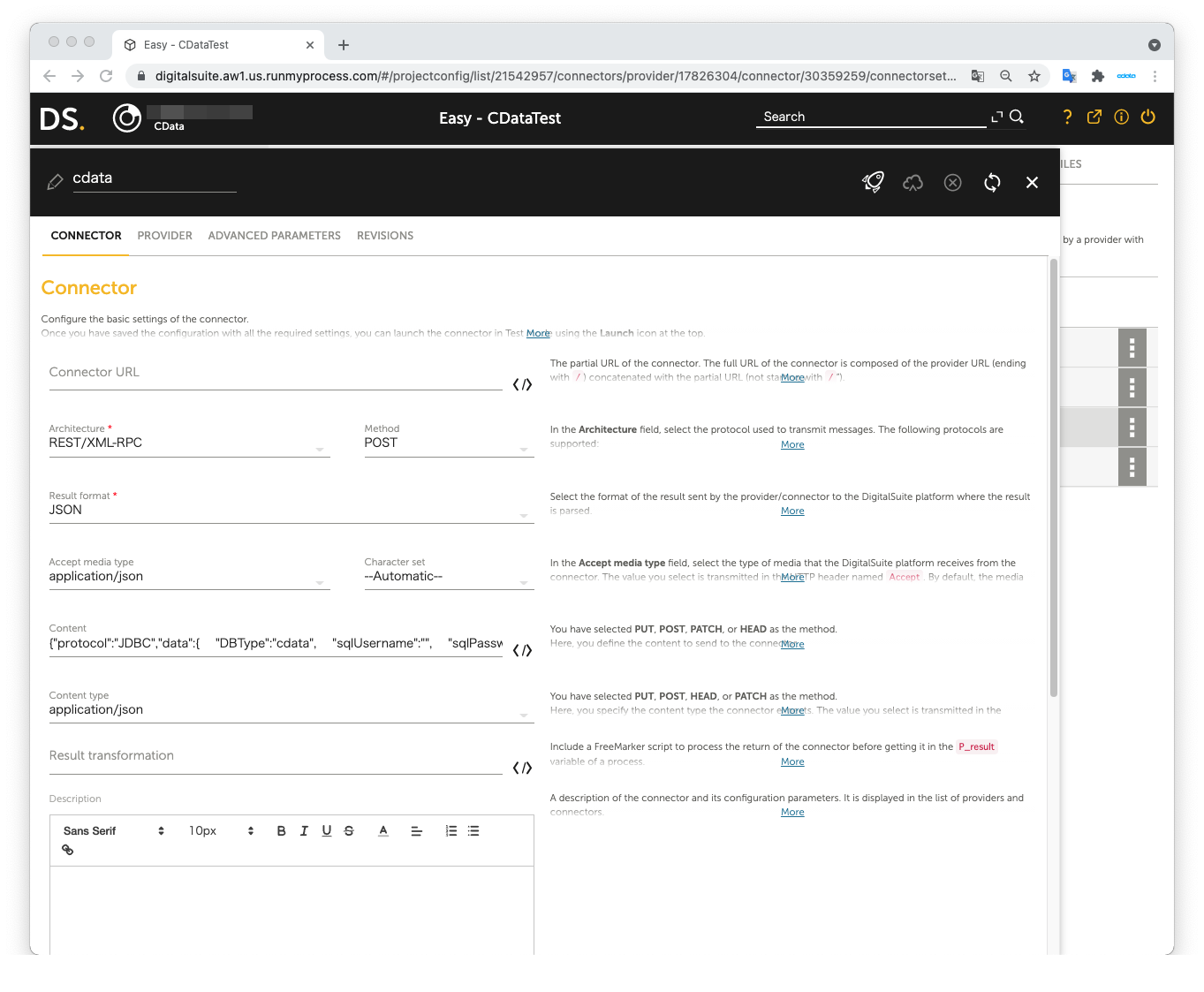
The JSON data we used as the Request body in JDBC Adapter:
{
"protocol":"JDBC",
"data":{
"DBType":"AmazonAthena",
"sqlUsername":"",
"sqlPassword":"",
"sqlStatement":"SELECT * FROM Customers"
}
}
Open Launch Test to perform the test. The test is successful if Amazon Athena data is shown in Result on the right pane.
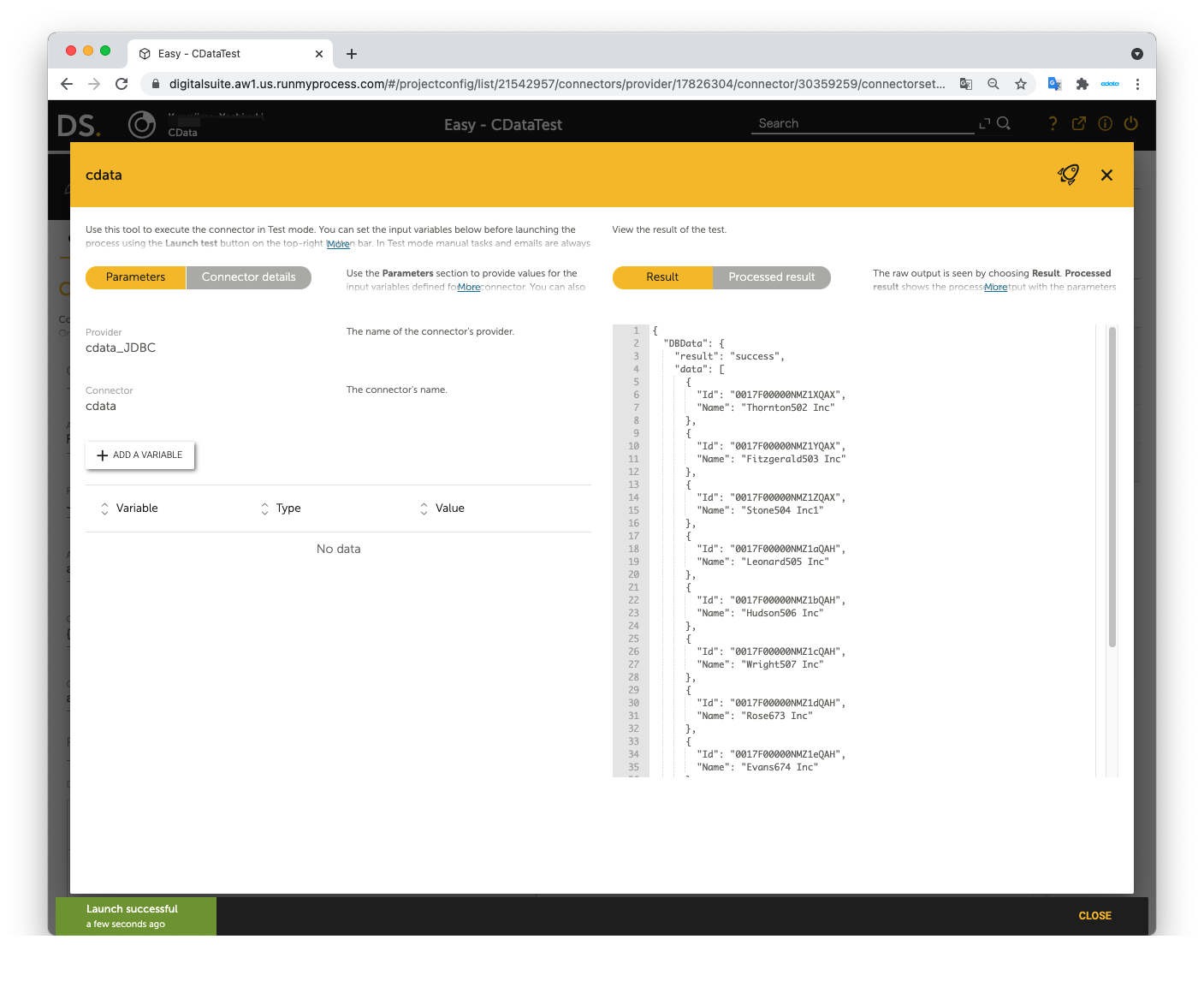
Now you can use Amazon Athena data in RunMyProcess DigitalSuite Studio through DSEC.
For the detailed information on supported SQL commands, refer to the SQL Compliance section in our help documentation. For information on tables, refer to the Data Model section.