Discover how a bimodal integration strategy can address the major data management challenges facing your organization today.
Get the Report →How to connect PolyBase to Amazon Athena
Use CData drivers and PolyBase to create an external data source in SQL Server 2019 with access to live Amazon Athena data.
PolyBase for SQL Server allows you to query external data by using the same Transact-SQL syntax used to query a database table. When paired with the CData ODBC Driver for Amazon Athena, you get access to your Amazon Athena data directly alongside your SQL Server data. This article describes creating an external data source and external tables to grant access to live Amazon Athena data using T-SQL queries.
NOTE: PolyBase is only available on SQL Server 19 and above, and only for Standard SQL Server.
The CData ODBC drivers offer unmatched performance for interacting with live Amazon Athena data using PolyBase due to optimized data processing built into the driver. When you issue complex SQL queries from SQL Server to Amazon Athena, the driver pushes down supported SQL operations, like filters and aggregations, directly to Amazon Athena and utilizes the embedded SQL engine to process unsupported operations (often SQL functions and JOIN operations) client-side. And with PolyBase, you can also join SQL Server data with Amazon Athena data, using a single query to pull data from distributed sources.
Connect to Amazon Athena
If you have not already, first specify connection properties in an ODBC DSN (data source name). This is the last step of the driver installation. You can use the Microsoft ODBC Data Source Administrator to create and configure ODBC DSNs. To create an external data source in SQL Server using PolyBase, configure a System DSN (CData Amazon Athena Sys is created automatically).
Authenticating to Amazon Athena
To authorize Amazon Athena requests, provide the credentials for an administrator account or for an IAM user with custom permissions: Set AccessKey to the access key Id. Set SecretKey to the secret access key.
Note: Though you can connect as the AWS account administrator, it is recommended to use IAM user credentials to access AWS services.
Obtaining the Access Key
To obtain the credentials for an IAM user, follow the steps below:
- Sign into the IAM console.
- In the navigation pane, select Users.
- To create or manage the access keys for a user, select the user and then select the Security Credentials tab.
To obtain the credentials for your AWS root account, follow the steps below:
- Sign into the AWS Management console with the credentials for your root account.
- Select your account name or number and select My Security Credentials in the menu that is displayed.
- Click Continue to Security Credentials and expand the Access Keys section to manage or create root account access keys.
Authenticating from an EC2 Instance
If you are using the CData Data Provider for Amazon Athena 2018 from an EC2 Instance and have an IAM Role assigned to the instance, you can use the IAM Role to authenticate. To do so, set UseEC2Roles to true and leave AccessKey and SecretKey empty. The CData Data Provider for Amazon Athena 2018 will automatically obtain your IAM Role credentials and authenticate with them.
Authenticating as an AWS Role
In many situations it may be preferable to use an IAM role for authentication instead of the direct security credentials of an AWS root user. An AWS role may be used instead by specifying the RoleARN. This will cause the CData Data Provider for Amazon Athena 2018 to attempt to retrieve credentials for the specified role. If you are connecting to AWS (instead of already being connected such as on an EC2 instance), you must additionally specify the AccessKey and SecretKey of an IAM user to assume the role for. Roles may not be used when specifying the AccessKey and SecretKey of an AWS root user.
Authenticating with MFA
For users and roles that require Multi-factor Authentication, specify the MFASerialNumber and MFAToken connection properties. This will cause the CData Data Provider for Amazon Athena 2018 to submit the MFA credentials in a request to retrieve temporary authentication credentials. Note that the duration of the temporary credentials may be controlled via the TemporaryTokenDuration (default 3600 seconds).
Connecting to Amazon Athena
In addition to the AccessKey and SecretKey properties, specify Database, S3StagingDirectory and Region. Set Region to the region where your Amazon Athena data is hosted. Set S3StagingDirectory to a folder in S3 where you would like to store the results of queries.
If Database is not set in the connection, the data provider connects to the default database set in Amazon Athena.
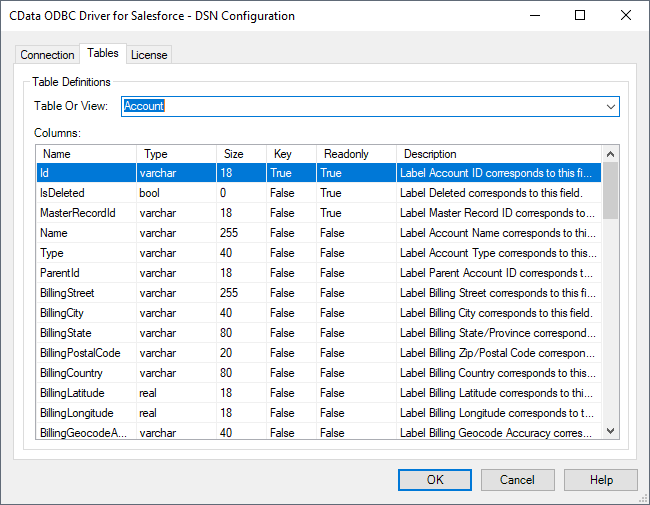
Click "Test Connection" to ensure that the DSN is connected to Amazon Athena properly. Navigate to the Tables tab to review the table definitions for Amazon Athena.
Create an External Data Source for Amazon Athena Data
After configuring the connection, you need to create a master encryption key and a credential database for the external data source.
Creating a Master Encryption Key
Execute the following SQL command to create a new master key, 'ENCRYPTION,' to encrypt the credentials for the external data source.
CREATE MASTER KEY ENCRYPTION BY PASSWORD = 'password';
Creating a Credential Database
Execute the following SQL command to create credentials for the external data source connected to Amazon Athena data.
NOTE: Since Amazon Athena does not require a User or Password to authenticate, you may use whatever values you wish for IDENTITY and SECRET.
CREATE DATABASE SCOPED CREDENTIAL amazonathena_creds WITH IDENTITY = 'username', SECRET = 'password';
Create an External Data Source for Amazon Athena
Execute a CREATE EXTERNAL DATA SOURCE SQL command to create an external data source for Amazon Athena with PolyBase:
- Set the LOCATION parameter , using the DSN and credentials configured earlier.
For Amazon Athena, set SERVERNAME to the URL or address for your server (e.g. 'localhost' or '127.0.0.1' for local servers; the remote URL for remote servers). Leave PORT empty. PUSHDOWN is set to ON by default, meaning the ODBC Driver can leverage server-side processing for complex queries.
CREATE EXTERNAL DATA SOURCE cdata_amazonathena_source WITH ( LOCATION = 'odbc://SERVER_URL', CONNECTION_OPTIONS = 'DSN=CData Amazon Athena Sys', -- PUSHDOWN = ON | OFF, CREDENTIAL = amazonathena_creds );
Create External Tables for Amazon Athena
After creating the external data source, use CREATE EXTERNAL TABLE statements to link to Amazon Athena data from your SQL Server instance. The table column definitions must match those exposed by the CData ODBC Driver for Amazon Athena. You can refer to the Tables tab of the DSN Configuration Wizard to see the table definition.
Sample CREATE TABLE Statement
The statement to create an external table based on a Amazon Athena Customers would look similar to the following:
CREATE EXTERNAL TABLE Customers( Name [nvarchar](255) NULL, TotalDue [nvarchar](255) NULL, ... ) WITH ( LOCATION='Customers', DATA_SOURCE=cdata_amazonathena_source );
Having created external tables for Amazon Athena in your SQL Server instance, you are now able to query local and remote data simultaneously. Thanks to built-in query processing in the CData ODBC Driver, you know that as much query processing as possible is being pushed to Amazon Athena, freeing up local resources and computing power. Download a free, 30-day trial of the ODBC Driver for Amazon Athena and start working with live Amazon Athena data alongside your SQL Server data today.